F1000-E防火墙透明模式配置
- 2关注
- 1收藏,2748浏览
最佳答案

可以大致参考:https://www.h3c.com/cn/d_201505/869008_30005_0.htm
可能稍微有点复杂,理解一下,其他双机热备的部分可以不参考
- 2021-06-25回答
- 评论(0)
- 举报
-
(1)

您好,请知:
以下是防火墙透明模式的配置案例,请参考:

组网说明:
本案例采用H3C HCL模拟器的F1060防火墙来模拟防火墙的透明模式典型组网配置2。为了实现PC之间相互PING通,因此需要在SW1、R1之间通过路由指向来实现路由可达。F1060处在R1、SW1之间,所以将F1060配置为透明模式,采用trunk的方式为R1、SW1透传业务。
配置步骤
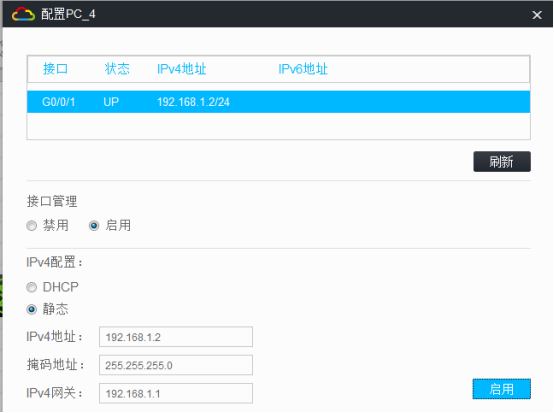
1、按照网络拓扑图正确配置IP地址
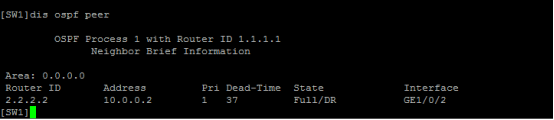
2、R1与SW1之间运行ospf路由协议
3、将F1060防火墙配置为透明模式,采用trunk的方式为R1、SW1透传业务。
配置关键点
SW1:
<H3C>sys
System View: return to User View with Ctrl+Z.
[H3C]sysname SW1
[SW1]vlan 100
[SW1-vlan100]quit
[SW1]int vlan 100
[SW1-Vlan-interface100]ip address 172.16.1.1 24
[SW1-Vlan-interface100]quit
[SW1]int gi 1/0/1
[SW1-GigabitEthernet1/0/1]port link-type access
[SW1-GigabitEthernet1/0/1]port access vlan 100
[SW1-GigabitEthernet1/0/1]quit
[SW1]vlan 10
[SW1-vlan10]quit
[SW1]int vlan 10
[SW1-Vlan-interface10]ip address 10.0.0.1 30
[SW1-Vlan-interface10]quit
[SW1]int gi 1/0/2
[SW1-GigabitEthernet1/0/2]des <connect to FW1>
[SW1-GigabitEthernet1/0/2]port link-type trunk
[SW1-GigabitEthernet1/0/2]undo port trunk permit vlan 1
[SW1-GigabitEthernet1/0/2]port trunk permit vlan 10
[SW1-GigabitEthernet1/0/2]quit
[SW1]int loopback 0
[SW1-LoopBack0]ip address 1.1.1.1 32
[SW1-LoopBack0]quit
[SW1]ospf 1 router-id 1.1.1.1
[SW1-ospf-1]area 0.0.0.0
[SW1-ospf-1-area-0.0.0.0]network 10.0.0.1 0.0.0.0
[SW1-ospf-1-area-0.0.0.0]network 1.1.1.1 0.0.0.0
[SW1-ospf-1-area-0.0.0.0]network 172.16.1.0 0.0.0.255
[SW1-ospf-1-area-0.0.0.0]quit
[SW1-ospf-1]quit
[SW1]
R1:
<H3C>sys
System View: return to User View with Ctrl+Z.
[H3C]sysname R1
[R1]int loopback 0
[R1-LoopBack0]ip address 2.2.2.2 32
[R1-LoopBack0]quit
[R1]int gi 0/1
[R1-GigabitEthernet0/1]ip address 192.168.1.1 24
[R1-GigabitEthernet0/1]quit
[R1]vlan 10
[R1-vlan10]quit
[R1]int vlan 10
[R1-Vlan-interface10]ip address 10.0.0.2 30
[R1-Vlan-interface10]quit
[R1]int gi 0/0
[R1-GigabitEthernet0/0]port link-mode bridge
[R1-GigabitEthernet0/0]port link-type trunk
[R1-GigabitEthernet0/0]undo port trunk permit vlan 1
[R1-GigabitEthernet0/0]port trunk permit vlan 10
[R1-GigabitEthernet0/0]quit
[R1]ospf 1 router-id 2.2.2.2
[R1-ospf-1]area 0.0.0.0
[R1-ospf-1-area-0.0.0.0]network 10.0.0.2 0.0.0.0
[R1-ospf-1-area-0.0.0.0]network 2.2.2.2 0.0.0.0
[R1-ospf-1-area-0.0.0.0]network 192.168.1.0 0.0.0.255
[R1-ospf-1-area-0.0.0.0]quit
[R1-ospf-1]quit
FW1 透明模式配置关键点:
<H3C>sys
System View: return to User View with Ctrl+Z.
[H3C]sysname FW1
[FW1]vlan 10
[FW1-vlan10]quit
[FW1]int range gi 1/0/2 to gi 1/0/3
[FW1-if-range]port link-mode bridge
[FW1-if-range]port link-type trunk
[FW1-if-range]undo port trunk permit vlan 1
[FW1-if-range]port trunk permit vlan 10
[FW1-if-range]quit
[FW1]security-zone name Trust
[FW1-security-zone-Trust]import interface GigabitEthernet 1/0/3 vlan 10
[FW1-security-zone-Trust]quit
[FW1]security-zone name Untrust
[FW1-security-zone-Untrust]import interface GigabitEthernet 1/0/2 vlan 10
[FW1-security-zone-Untrust]quit
[FW1]acl basic 2002
[FW1-acl-ipv4-basic-2002]rule 0 permit source any
[FW1-acl-ipv4-basic-2002]quit
[FW1]
[FW1]zone-pair security source trust destination untrust
[FW1-zone-pair-security-Trust-Untrust]packet-filter 2002
[FW1-zone-pair-security-Trust-Untrust]quit
[FW1]
[FW1]zone-pair security source untrust destination trust
[FW1-zone-pair-security-Untrust-Trust]packet-filter 2002
[FW1-zone-pair-security-Untrust-Trust]quit
[FW1]
[FW1]zone-pair security source trust destination local
[FW1-zone-pair-security-Trust-Local]packet-filter 2002
[FW1-zone-pair-security-Trust-Local]quit
[FW1]
[FW1]zone-pair security source local destination trust
[FW1-zone-pair-security-Local-Trust]packet-filter 2002
[FW1-zone-pair-security-Local-Trust]quit
[FW1]
[FW1]zone-pair security source untrust destination local
[FW1-zone-pair-security-Untrust-Local]packet-filter 2002
[FW1-zone-pair-security-Untrust-Local]quit
[FW1]
[FW1]zone-pair security source local destination untrust
[FW1-zone-pair-security-Local-Untrust]packet-filter 2002
[FW1-zone-pair-security-Local-Untrust]quit
[FW1]
[FW1]zone-pair security source trust destination trust
[FW1-zone-pair-security-Trust-Trust]packet-filter 2002
[FW1-zone-pair-security-Trust-Trust]quit
[FW1]
[FW1]zone-pair security source untrust destination untrust
[FW1-zone-pair-security-Untrust-Untrust]packet-filter 2002
[FW1-zone-pair-security-Untrust-Untrust]quit
测试:
所有PC都填写IP地址:

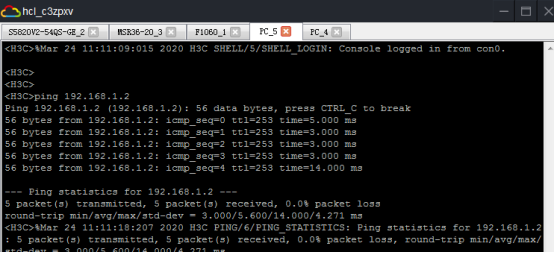
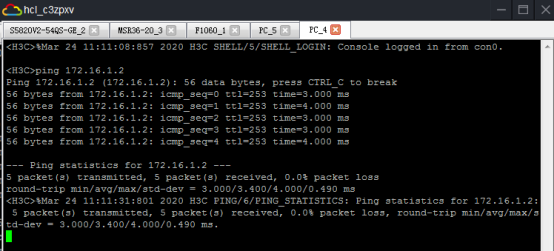
PC之间可以相互PING通:
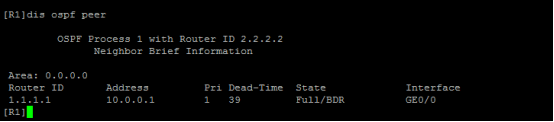
分别查看SW1、R1的OSPF邻居信息:
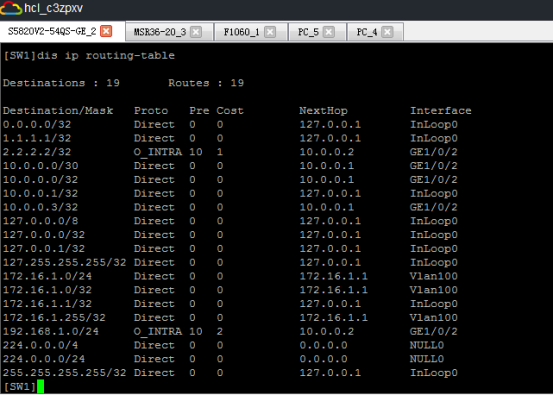
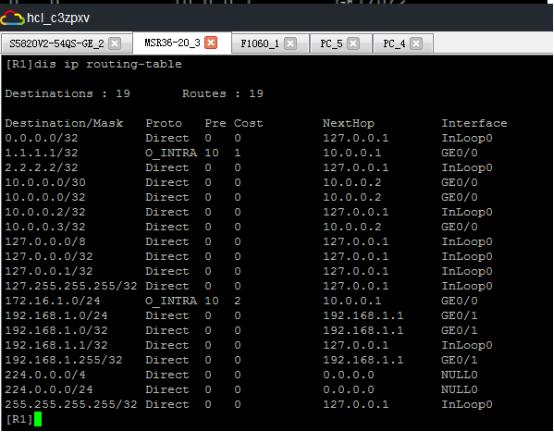
分别查看SW1、R1的路由表:
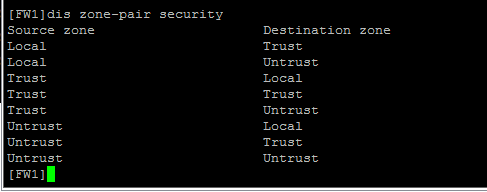
查看FW1的zone-pair:
- 2021-06-25回答
- 评论(0)
- 举报
-
(0)
暂无评论

防火墙透明部署非常简单
1、把物理口配置成二层口
2、配置一个BVI接口,二层口都加入这个BVI
3、不同的二层口加入到不同的域
4、配置相应的域间策略即可
- 2021-06-25回答
- 评论(0)
- 举报
-
(0)
暂无评论


| # | |
| vlan 1 | |
| int vlan 1 | |
| ip add 192.168.10.2 24 | 管理地址,根据实际需要设置 |
| # | |
| int range g1/0/1 g1/0/2 | |
| port link-mode bridge | |
| # | |
| security-zone name Untrust | |
| import int g1/0/1 vlan 1 to 4094 | |
| # | |
| security-zone name Trust | |
| import interface Vlan-interface1 | |
| import int g1/0/2 vlan 1 to 4094 | |
| # | |
| security-policy ip | |
| rule 0 name shangwang1 | |
| action pass | |
| source-zone Trust | |
| destination-zone Untrust | |
| rule 1 name shangwang2 | |
| action pass | |
| source-zone Untrust | |
| destination-zone Trust | |
| rule 2 name trust-local | |
| action pass | |
| source-zone trust | |
| destination-zone local | |
| # | |
| acl advanced 3000 | |
| rule 0 permit ip | |
| # | |
| zone-pair security source Trust destination Untrust | |
| packet-filter 3000 | |
| # | |
| zone-pair security source Trust destination Local | |
| packet-filter 3000 | |
| # | |
| zone-pair security source Local destination Trust | |
| packet-filter 3000 | |
| # | |
| zone-pair security source Untrust destination Trust | |
| packet-filter 3000 | |
| # | |
| zone-pair security source Untrust destination Local | |
| packet-filter 3000 | |
| # | |
| zone-pair security source Local destination Untrust | |
| packet-filter 3000 | |
| # | |
| sa f |
- 2021-06-25回答
- 评论(0)
- 举报
-
(0)
暂无评论

这款墙的透明模式,进入接口下直接改成二层模式即可
inter GigabitEthernet0/1
port link-mode bridge
其它配置,和三层模式配置方法一样,比如将端口加入安全域、域间策略,二层模式和三层模式配置方式和思路都一样的
- 2021-06-26回答
- 评论(0)
- 举报
-
(0)
暂无评论

配置H3C入门级防火墙透明模式
基础参数
以下是为 H3C SecPath 防火墙(V7.0)配置透明模式并激活 WEB 登录功能的初始化配置步骤,基于提供的网络参数:
网络: 192.168.100.0/24
上联接口: GigabitEthernet 1/0/0,连接至主路由(192.168.100.1)
下联接口: GigabitEthernet 1/0/8,连接至下游设备(192.168.100.8)
防火墙管理 IP: 192.168.100.246/24
以下配置假设通过 CLI(命令行界面)进行,并确保防火墙工作在透明模式(二层模式)。
配置明细-第一段-基础配置
创建VLAN100并配置IP
默认VLAN1不支持配置IP
<H3C>system-viewSystem View: return to User View with Ctrl+Z.
[H3C]vlan 100
[H3C-vlan100]exit
[H3C]interface Vlan-interface 100
[H3C-Vlan-interface100]ip address 192.168.100.246 24
[H3C-Vlan-interface100]exit
配置接出口模式并加入VLAN
[H3C]interface range GigabitEthernet 1/0/0 GigabitEthernet 1/0/8[H3C-if-range]port link-mode bridge
[H3C-if-range]port access vlan 100
[H3C-if-range]quit
配置安全区绑定VLAN
上联接口配置为Untrust区
上联接口: GigabitEthernet 1/0/0,连接至主路由(192.168.100.1)
[H3C]security-zone name Untrust[H3C-security-zone-Untrust]import interface GigabitEthernet 1/0/0 vlan 1 to 4094
[H3C-security-zone-Untrust]quit
[H3C]
下联接口和VLAN桥接口配置为Trust区
下联接口: GigabitEthernet 1/0/8,连接至下游设备(192.168.100.8)
[H3C]security-zone name Trust[H3C-security-zone-Trust]import interface GigabitEthernet 1/0/8
Please specify a VLAN list for the layer 2 interface.#需要绑定VLAN
[H3C-security-zone-Trust]import interface GigabitEthernet 1/0/8 vlan 1 to 4094
[H3C-security-zone-Trust]import interface Vlan-interface 100
[H3C-security-zone-Trust]quit
[H3C]
配置上联默认路由指向主路由器
[H3C]ip route-static 0.0.0.0 0.0.0.0 192.168.100.1启用HTTP/HTTPS服务
[H3C]ip http enable[H3C]ip https enable
配置WEB登录用户
修改默认用户密码并配置权限及使用服务
[H3C]local-user admin
[H3C-luser-manage-admin]password simple **********
[H3C-luser-manage-admin]service-type http https telnet ssh
[H3C-luser-manage-admin]authorization-attribute user-role level-15
[H3C-luser-manage-admin]quit
创建新用户并配置权限及使用服务
[H3C]local-user IT class manage
New local user added.
[H3C-luser-manage-IT]password simple **********
[H3C-luser-manage-IT]service-type http https telnet ssh terminal
[H3C-luser-manage-IT]authorization-attribute user-role level-15
[H3C-luser-manage-IT]authorization-attribute user-role network-admin
[H3C-luser-manage-IT]quit
[H3C]
配置明细-第二段-各安全区互联
TRUST-UNTRUST互联
[H3C]security-policy ip[H3C-security-policy-ip]rule 0 name TRUST-UNTRUST
[H3C-security-policy-ip-0-TRUST-UNTRUST]action pass
[H3C-security-policy-ip-0-TRUST-UNTRUST]source-zone Trust
[H3C-security-policy-ip-0-TRUST-UNTRUST]destination-zone Untrust
[H3C-security-policy-ip-0-TRUST-UNTRUST]quit
[H3C-security-policy-ip]
UNTRUST-TRUST互联
[H3C-security-policy-ip]rule 1 name UNTRUST-TRUST[H3C-security-policy-ip-1-UNTRUST-TRUST]action pass
[H3C-security-policy-ip-1-UNTRUST-TRUST]source-zone Untrust
[H3C-security-policy-ip-1-UNTRUST-TRUST]destination-zone Trust
[H3C-security-policy-ip-1-UNTRUST-TRUST]quit
[H3C-security-policy-ip]
TRUST-LOCAL互联
[H3C-security-policy-ip][H3C-security-policy-ip]rule 2 name TRUST-LOCAL
[H3C-security-policy-ip-2-TRUST-LOCAL]action pass
[H3C-security-policy-ip-2-TRUST-LOCAL]source-zone Trust
[H3C-security-policy-ip-2-TRUST-LOCAL]destination-zone Local
[H3C-security-policy-ip-2-TRUST-LOCAL]quit
[H3C-security-policy-ip]
[H3C-security-policy-ip]quit
[H3C]
配置明细-第三段-各安全区互联放行
ACL建立
[H3C]acl advanced 3000[H3C-acl-ipv4-adv-3000]rule 0 permit ip
[H3C-acl-ipv4-adv-3000]quit
[H3C]
放行Trust-Untrust
[H3C]zone-pair security source Trust destination Untrust[H3C-zone-pair-security-Trust-Untrust]packet-filter 3000
[H3C-zone-pair-security-Trust-Untrust]quit
[H3C]
放行Untrust-Trust
[H3C]zone-pair security source Untrust destination Trust[H3C-zone-pair-security-Untrust-Trust]packet-filter 3000
[H3C-zone-pair-security-Untrust-Trust]quit
[H3C]
放行Trust-Local
[H3C]zone-pair security source Trust destination Local[H3C-zone-pair-security-Trust-Local]packet-filter 3000
[H3C-zone-pair-security-Trust-Local]quit
[H3C]
放行Local-Trust
[H3C]zone-pair security source Local destination Trust[H3C-zone-pair-security-Local-Trust]packet-filter 3000
[H3C-zone-pair-security-Local-Trust]quit
[H3C]
放行Untrust-Local
[H3C]zone-pair security source Untrust destination Local[H3C-zone-pair-security-Untrust-Local]packet-filter 3000
[H3C-zone-pair-security-Untrust-Local]quit
[H3C]
放行Local-Untrust
[H3C]zone-pair security source Local destination Untrust[H3C-zone-pair-security-Local-Untrust]packet-filter 3000
[H3C-zone-pair-security-Local-Untrust]quit
[H3C]
检查配置明细写入保存
检查配置明细
[H3C]display current-configuration#
version 7.1.064, Release 8860P41
#
sysname H3C
#
clock protocol none
#
irf mac-address persistent timer
irf auto-update enable
undo irf link-delay
irf member 1 priority 1
#
dns server 8.8.8.8
dns server 114.114.114.114
#
password-recovery enable
#
vlan 1
#
vlan 100
#
interface NULL0
#
interface Vlan-interface100
ip address 192.168.100.246 255.255.255.0
#
interface GigabitEthernet1/0/1
port link-mode route
#
interface GigabitEthernet1/0/2
port link-mode route
#
interface GigabitEthernet1/0/3
port link-mode route
#
interface GigabitEthernet1/0/4
port link-mode route
#
interface GigabitEthernet1/0/5
port link-mode route
#
interface GigabitEthernet1/0/6
port link-mode route
#
interface GigabitEthernet1/0/7
port link-mode route
#
interface GigabitEthernet1/0/9
port link-mode route
#
interface GigabitEthernet1/0/10
port link-mode route
#
interface GigabitEthernet1/0/11
port link-mode route
#
interface GigabitEthernet1/0/0
port link-mode bridge
port access vlan 100
#
interface GigabitEthernet1/0/8
port link-mode bridge
port access vlan 100
#
security-zone name Local
#
security-zone name Trust
import interface Vlan-interface100
import interface GigabitEthernet1/0/8 vlan 1 to 4094
#
security-zone name DMZ
#
security-zone name Untrust
import interface GigabitEthernet1/0/0 vlan 1 to 4094
#
security-zone name Management
#
zone-pair security source Local destination Trust
packet-filter 3000
#
zone-pair security source Local destination Untrust
packet-filter 3000
#
zone-pair security source Trust destination Local
packet-filter 3000
#
zone-pair security source Trust destination Untrust
packet-filter 3000
#
zone-pair security source Untrust destination Local
packet-filter 3000
#
zone-pair security source Untrust destination Trust
packet-filter 3000
#
scheduler logfile size 16
#
line class aux
user-role network-operator
#
line class console
authentication-mode scheme
user-role network-admin
#
line class vty
user-role network-operator
#
line aux 0
authentication-mode none
user-role network-admin
#
line con 0
user-role network-admin
#
line vty 0 63
authentication-mode scheme
user-role network-admin
#
ip route-static 0.0.0.0 0 192.168.100.1
#
performance-management
#
ssh server enable
#
acl advanced 3000
rule 0 permit ip
#
undo password-control blacklist all-line
#
domain system
#
domain default enable system
#
role name level-0
description Predefined level-0 role
#
role name level-1
description Predefined level-1 role
#
role name level-2
description Predefined level-2 role
#
role name level-3
description Predefined level-3 role
#
role name level-4
description Predefined level-4 role
#
role name level-5
description Predefined level-5 role
#
role name level-6
description Predefined level-6 role
#
role name level-7
description Predefined level-7 role
#
role name level-8
description Predefined level-8 role
#
role name level-9
description Predefined level-9 role
#
role name level-10
description Predefined level-10 role
#
role name level-11
description Predefined level-11 role
#
role name level-12
description Predefined level-12 role
#
role name level-13
description Predefined level-13 role
#
role name level-14
description Predefined level-14 role
#
user-group system
#
local-user IT class manage
password hash $h$6$ep+a1CetbMFdhvE/$iXiGDUCViiZLNAePaSmarK050bvQPRflFEpB0H1J1BOyGuthHSVdePHdBHKB45C9T4IXOb5ZZTDgQIPK3UTrZw==
service-type ssh telnet termina http https
authorization-attribute user-role level-15
authorization-attribute user-role network-admin
authorization-attribute user-role network-operator
#
local-user admin class manage
password hash $h$6$QRZpQH7ack5KdbZT$7Cn8guOGEAys4Ibys1S9t4MOCarqZEZM7RzyNkSNTfSrGzbawE/3X3eN2rP5bRG4sRO4Lh+FQJnRTa+aK2BwCQ==
service-type ssh telnet terminal http https
authorization-attribute user-role level-3
authorization-attribute user-role level-15
authorization-attribute user-role network-admin
authorization-attribute user-role network-operator
#
ip http enable
ip https enable
#
loadbalance isp file flash:/lbispinfo_v1.5.tp
#
security-policy ip
rule 0 name TRUST-UNTRUST
action pass
source-zone Trust
destination-zone Untrust
rule 1 name UNTRUST-TRUST
action pass
source-zone Untrust
destination-zone Trust
rule 2 name TRUST-LOCAL
action pass
source-zone Trust
destination-zone Local
#
cloud-management server domain opstunnel-seccloud.h3c.com
#
return
[H3C]
写入配置
[H3C]save forceValidating file. Please wait...
Saved the current configuration to mainboard device successfully.
[H3C]
本文注释
更新日期:2025年08月02日作成:Fisher
- 2025-08-02回答
- 评论(0)
- 举报
-
(0)
暂无评论
编辑答案


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明






暂无评论