MSR3600 IPSEC VPN
- 0关注
- 1收藏,1548浏览
问题描述:
对齐方式
- 靠左
- 居中
- 靠右
问题
(1)该VPN用于分公司联系,原来一直正常,电信过来调试不小心改动。
(2)本地PPOE固定IP,对方固定 IP
(3)目前可以PING 对方IP,没有问题,但show ike sa 没有连接,VPN不正常
[H3C]show cur
#
version 7.1.064, Release 0605P21
#
sysname H3C
#
dialer-group 2 rule ip permit
#
dhcp server always-broadcast
#
dns proxy enable
#
password-recovery enable
#
vlan 1
#
vlan 100
#
dhcp server ip-pool lan1
gateway-list 192.168.0.1
network 192.168.0.0 mask 255.255.254.0
address range 192.168.1.2 192.168.1.254
dns-list 192.168.0.1
#
controller Cellular0/0
#
interface Aux0
#
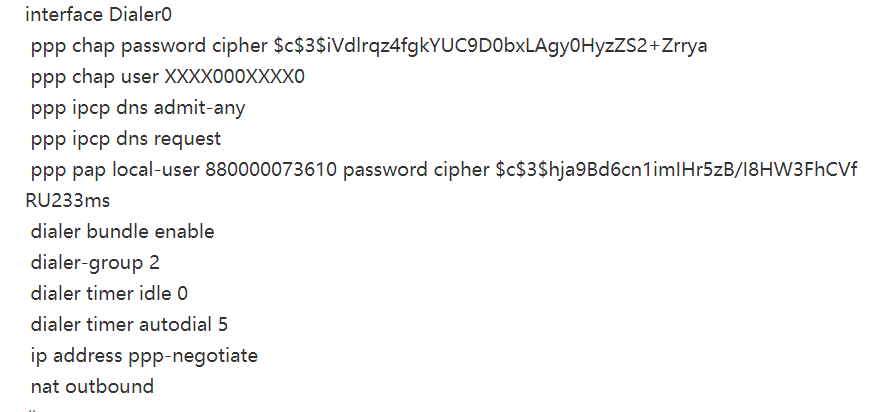
interface Dialer0
ppp chap password cipher $c$3$iVdlrqz4fgkYUC9D0bxLAgy0HyzZS2+Zrrya
ppp chap user XXXX000XXXX0
ppp ipcp dns admit-any
ppp ipcp dns request
ppp pap local-user 880000073610 password cipher $c$3$hja9Bd6cn1imIHr5zB/I8HW3FhCVfRU233ms
dialer bundle enable
dialer-group 2
dialer timer idle 0
dialer timer autodial 5
ip address ppp-negotiate
nat outbound
#
interface Dialer2
dialer bundle enable
#
interface NULL0
#
interface Vlan-interface1
ip address 192.168.0.1 255.255.254.0
tcp mss 1280
#
interface Vlan-interface100
mtu 1300
ip address 192.188.2.98 255.255.255.0
tcp mss 1024
#
interface GigabitEthernet0/0
port link-mode route
mtu 1300
tcp mss 1024
pppoe-client dial-bundle-number 0
pppoe-client dial-bundle-number 2
ipsec apply policy poli
#
interface GigabitEthernet0/1
port link-mode route
#
interface GigabitEthernet0/2
port link-mode route
#
interface GigabitEthernet0/27
port link-mode route
#
interface GigabitEthernet0/3
port link-mode bridge
port access vlan 100
#
interface GigabitEthernet0/4
port link-mode bridge
port access vlan 100
#
interface GigabitEthernet0/5
port link-mode bridge
port access vlan 100
#
interface GigabitEthernet0/6
port link-mode bridge
port access vlan 100
#
interface GigabitEthernet0/7
port link-mode bridge
port access vlan 100
#
interface GigabitEthernet0/8
port link-mode bridge
port access vlan 100
#
interface GigabitEthernet0/9
port link-mode bridge
port access vlan 100
#
interface GigabitEthernet0/10
port link-mode bridge
port access vlan 100
#
interface GigabitEthernet0/11
port link-mode bridge
port access vlan 100
#
interface GigabitEthernet0/12
port link-mode bridge
port access vlan 100
#
interface GigabitEthernet0/13
port link-mode bridge
port access vlan 100
#
interface GigabitEthernet0/14
port link-mode bridge
port access vlan 100
#
interface GigabitEthernet0/15
port link-mode bridge
port access vlan 100
#
interface GigabitEthernet0/16
port link-mode bridge
port access vlan 100
#
interface GigabitEthernet0/17
port link-mode bridge
port access vlan 100
#
interface GigabitEthernet0/18
port link-mode bridge
port access vlan 100
#
interface GigabitEthernet0/19
port link-mode bridge
port access vlan 100
#
interface GigabitEthernet0/20
port link-mode bridge
port access vlan 100
#
interface GigabitEthernet0/21
port link-mode bridge
port access vlan 100
#
interface GigabitEthernet0/22
port link-mode bridge
port access vlan 100
#
interface GigabitEthernet0/23
port link-mode bridge
port access vlan 100
#
interface GigabitEthernet0/24
port link-mode bridge
port access vlan 100
#
interface GigabitEthernet0/25
port link-mode bridge
port access vlan 100
#
interface GigabitEthernet0/26
port link-mode bridge
port access vlan 100
#
scheduler logfile size 16
#
line class aux
user-role network-admin
#
line class tty
user-role network-operator
#
line class vty
user-role network-operator
#
line aux 0
user-role network-admin
#
line vty 0 63
authentication-mode scheme
user-role network-operator
#
ip route-static 0.0.0.0 0 Dialer0
#
acl advanced 3000
rule 0 permit ip source 192.188.2.0 0.0.0.255 destination 192.188.1.0 0.0.0.255
#
acl advanced 3001
rule 0 deny ip source 192.188.2.0 0.0.0.255 destination 192.188.1.0 0.0.0.255
rule 10 permit ip
#
password-control enable
undo password-control aging enable
undo password-control history enable
password-control length 6
password-control login-attempt 3 exceed lock-time 10
password-control update-interval 0
password-control login idle-time 0
password-control complexity user-name check
#
domain system
#
domain default enable system
#
role name level-0
description Predefined level-0 role
#
role name level-1
description Predefined level-1 role
#
role name level-2
description Predefined level-2 role
#
role name level-3
description Predefined level-3 role
#
role name level-4
description Predefined level-4 role
#
role name level-5
description Predefined level-5 role
#
role name level-6
description Predefined level-6 role
#
role name level-7
description Predefined level-7 role
#
role name level-8
description Predefined level-8 role
#
role name level-9
description Predefined level-9 role
#
role name level-10
description Predefined level-10 role
#
role name level-11
description Predefined level-11 role
#
role name level-12
description Predefined level-12 role
#
role name level-13
description Predefined level-13 role
#
role name level-14
description Predefined level-14 role
#
user-group system
#
local-user admin class manage
service-type telnet http
authorization-attribute user-role network-admin
#
ipsec transform-set trans
esp encryption-algorithm 3des-cbc
esp authentication-algorithm md5
#
ipsec policy poli 1 isakmp
transform-set trans
security acl 3000
remote-address XXX.XX.XXX.4
ike-profile prof
#
ike profile prof
keychain keyq
match remote identity address XXX.XX.XXX.4 255.255.255.0
proposal 1
#
ike proposal 1
encryption-algorithm 3des-cbc
dh group5
authentication-algorithm md5
#
ike keychain keyq
pre-shared-key address XXX.XX.XXX.4 255.255.255.0 key cipher $c$3$DRPz8/Vvo1+MoZgPro7Hqtb9wfm+R0LtWdNCFUB1+g==
#
ip http enable
#
wlan global-configuration
control-address disable
#
wlan ap-group default-group
#
cloud-management server domain oasis.h3c.com
#
组网及组网描述:
- 2021-10-11提问
- 举报
-
(0)
最佳答案

IPSEC VPN故障排查:
1、检查公网地址的连通性
2、检查ipsec acl是否配置正确(两端ACL以互为镜像的方式配置)
3、检查ike keychain/ike profile 协商参数配置是否正确(工作模式、keychain、identity、本端/对端隧道地址或隧道名称、NAT穿越功能v7自适应)
4、检查ipsec proposal(v5平台) /ipsec transform-set(v7平台)参数两端是否一致(封装模式、安全协议、验证算法、加密算法)
5、检查设备是否创建ipsec策略,并加载协商参数(acl、ike profile 、ipsec transform-set、对端隧道IP)
6、检查ipsec策略是否应用在正确的接口上
IPSEC排查命令:
1、disp ipsec policy
2、disp acl
3、dis cu conf ike-profile
4、dis cu conf ike-keychain
5、display ike proposal
6、display ipsec transform-set
7、disp ike sa (verbose)
8、disp ipsec sa
9、reset ipsec sa
10、reset ike sa
- 2021-10-11回答
- 评论(1)
- 举报
-
(0)
对方IP能PING通,下一步查哪个


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明




对方IP能PING通,下一步查哪个