IKE起来了,IPSEC没起来,
- 0关注
- 1收藏,2666浏览
问题描述:
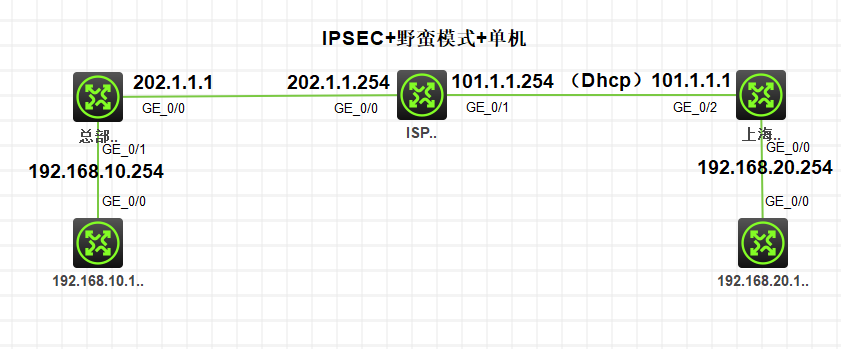
IKE起来了,IPSEC没起来,设备到公网都是通的,请看看问题出在哪里
总部:
interface GigabitEthernet0/0
ip address 202.1.1.1 255.255.255.0
nat outbound 3000
ipsec apply policy sh
# interface GigabitEthernet0/1
port link-mode route
combo enable copper
ip address 192.168.10.254 255.255.255.0
# ip route-static 0.0.0.0 0 202.1.1.254 #
acl advanced 3000 description "NAT"
rule 0 deny ip source 192.168.10.0 0.0.0.255 destination 192.168.20.0 0.0.0.255
rule 5 permit ip #
ipsec transform-set sh
esp encryption-algorithm 3des-cbc esp
authentication-algorithm md5
# ipsec policy sh 1 isakmp
transform-set sh
ike-profile sh
# ike identity fqdn bj
# ike profile sh
keychain sh
exchange-mode aggressive
match remote identity fqdn sh
proposal 1 #
ike proposal 1
encryption-algorithm 3des-cbc
authentication-algorithm md5
# ike keychain sh
pre-shared-key hostname sh key cipher $c$3$xnjT4ZikZ/ZopdbDuOfzuXrrW20veQ==
#
return
上海分部:
interface GigabitEthernet0/0
ip address 192.168.20.254 255.255.255.0
# interface GigabitEthernet0/2
ip address dhcp-alloc
nat outbound 3000
ipsec apply policy bj
# acl advanced 3000
rule 0 deny ip source 192.168.20.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
rule 10 permit ip #
acl advanced 3001
description "IPSEC"
rule 0 permit ip source 192.168.20.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
ipsec transform-set bj
esp encryption-algorithm
3des-cbc esp authentication-algorithm md5
# ipsec policy bj 1 isakmp
transform-set bj
security acl 3001
remote-address 202.1.1.1
ike-profile bj
# ike identity fqdn sh
# ike profile bj
keychain bj
exchange-mode aggressive match remote identity fqdn bj
proposal 1 # ike proposal 1
encryption-algorithm 3des-cbc
authentication-algorithm md5
# ike keychain bj pre-shared-key address 202.1.1.1 255.255.255.255 key cipher $c$3$4SoG6f4OnnAejmyQUkPsgDQhXuISxQ==
组网及组网描述:
设置列表
- 有序列表
- 无序列表
对齐方式
- 靠左
- 居中
- 靠右
- 2021-10-26提问
- 举报
-
(0)
最佳答案

IPSEC VPN故障排查:
1、检查公网地址的连通性
2、检查ipsec acl是否配置正确(两端ACL以互为镜像的方式配置)
3、检查ike keychain/ike profile 协商参数配置是否正确(工作模式、keychain、identity、本端/对端隧道地址或隧道名称、NAT穿越功能v7自适应)
4、检查ipsec proposal(v5平台) /ipsec transform-set(v7平台)参数两端是否一致(封装模式、安全协议、验证算法、加密算法)
5、检查设备是否创建ipsec策略,并加载协商参数(acl、ike profile 、ipsec transform-set、对端隧道IP)
6、检查ipsec策略是否应用在正确的接口上
IPSEC排查命令:
1、disp ipsec policy
2、disp acl
3、dis cu conf ike-profile
4、dis cu conf ike-keychain
5、display ike proposal
6、display ipsec transform-set
7、disp ike sa (verbose)
8、disp ipsec sa
9、reset ipsec sa
10、reset ike sa
- 2021-10-26回答
- 评论(1)
- 举报
-
(0)
就是检查没有问题,才发出来咨询


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明


就是检查没有问题,才发出来咨询