MSR系列路由器IPSEC VPN主模式配置
- 0关注
- 2收藏,2491浏览
问题描述:
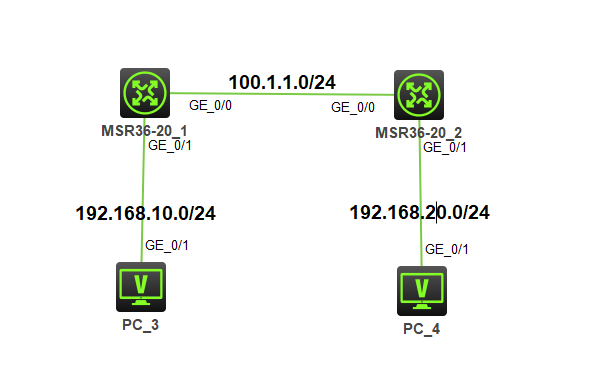
如图,两台路由器配置ipsec vpn,接口及相关配置后,发现ike sa都无法起来,如下为两台设备关键配置:
MSR36-20_1:
int g0/0
ip add 100.1.1.1 24
quit
int g0/1
ip add 192.168.10.254 24
quit
acl adv name ipsec_ip
rule permit ip source 192.168.10.0 0.0.0.255 dest 192.168.20.0 0.0.0.255
quit
acl adv name ipsec_ip_nonat
rule deny ip source 192.168.10.0 0.0.0.255 dest 192.168.20.0 0.0.0.255
ike proso 1
quit
ike ikechain
pre address 100.1.1.2 key simple 123456
quit
ike profile 1
keychain 1
proso 1
exchange main
match remote ident address 100.1.1.2
local-ident address 100.1.1.1
quit
ipsec trans 1
esp auth sha1
esp en aes-cbc-128
quit
ipsec policy ipsec 1 isakm
trans 1
ike profi 1
sec acl ipsec_ip
local-address 100.1.1.1
remote-address 100.1.1.2
quit
int g0/0
ipsec apply policy ipsec_ip
nat outbound ipsec_ip_nonat
MSR36-20_2:
int g0/0
ip add 100.1.1.2 24
int g0/1
ip add 192.168.20.254 24
quit
ike proso 1
quit
ike keychain 1
pre address 100.1.1.1 key simple 123456
quit
ike profile 1
keychain 1
prosol 1
exchan main
match remote iden address 100.1.1.1
local-ident address 100.1.1.2
ipsec trans 1
esp auth sha1
esp en aes-cbc-128
quit
ipsec policy ipsec isakm
ike profil 1
sec acl ipse_ip
trans 1
local-address 100.1.1.2
remote-address 100.1.1.1
quit
int g0/0
ipsec apply policy ipsec
nat outbound ipsec_ip_nonat
组网及组网描述:
- 2022-01-04提问
- 举报
-
(0)
最佳答案

RT1的ipsec policy绑定关系错误
int g0/0
ipsec apply policy ipsec_ip
- 2022-01-04回答
- 评论(1)
- 举报
-
(0)
是写错了,实际是策略名称是ipsec

路由写了吗?
就是ip route-static 192.168.20.0 24 100.1.1.2,对端同理。没有路由的话流量不会引到g0/0口上,也就不会触发IPSEC。
我的配置:

<R1>dis cur
#
version 7.1.064, Release 0821P11
#
sysname R1
#
system-working-mode standard
xbar load-single
password-recovery enable
lpu-type f-series
#
vlan 1
#
interface Serial1/0
#
interface Serial2/0
#
interface Serial3/0
#
interface Serial4/0
#
interface NULL0
#
interface GigabitEthernet0/0
port link-mode route
combo enable copper
ip address 100.1.1.1 255.255.255.0
nat outbound name ipsec_ip_nonat
ipsec apply policy ipsec_ip
#
interface GigabitEthernet0/1
port link-mode route
combo enable copper
ip address 192.168.10.254 255.255.255.0
#
interface GigabitEthernet0/2
port link-mode route
combo enable copper
#
interface GigabitEthernet5/0
port link-mode route
combo enable copper
#
interface GigabitEthernet5/1
port link-mode route
combo enable copper
#
interface GigabitEthernet6/0
port link-mode route
combo enable copper
#
interface GigabitEthernet6/1
port link-mode route
combo enable copper
#
scheduler logfile size 16
#
line class aux
user-role network-operator
#
line class console
user-role network-admin
#
line class tty
user-role network-operator
#
line class vty
user-role network-operator
#
line aux 0
user-role network-operator
#
line con 0
user-role network-admin
#
line vty 0 63
user-role network-operator
#
ip route-static 192.168.20.0 24 100.1.1.2
#
acl advanced name ipsec_ip
rule 0 permit ip source 192.168.10.0 0.0.0.255 destination 192.168.20.0 0.0.0.255
#
acl advanced name ipsec_ip_nonat
rule 0 deny ip source 192.168.10.0 0.0.0.255 destination 192.168.20.0 0.0.0.255
#
domain system
#
domain default enable system
#
role name level-0
description Predefined level-0 role
#
role name level-1
description Predefined level-1 role
#
role name level-2
description Predefined level-2 role
#
role name level-3
description Predefined level-3 role
#
role name level-4
description Predefined level-4 role
#
role name level-5
description Predefined level-5 role
#
role name level-6
description Predefined level-6 role
#
role name level-7
description Predefined level-7 role
#
role name level-8
description Predefined level-8 role
#
role name level-9
description Predefined level-9 role
#
role name level-10
description Predefined level-10 role
#
role name level-11
description Predefined level-11 role
#
role name level-12
description Predefined level-12 role
#
role name level-13
description Predefined level-13 role
#
role name level-14
description Predefined level-14 role
#
user-group system
#
ipsec transform-set 1
esp encryption-algorithm aes-cbc-128
esp authentication-algorithm sha1
#
ipsec policy ipsec_ip 1 isakmp
transform-set 1
security acl name ipsec_ip
local-address 100.1.1.1
remote-address 100.1.1.2
ike-profile 1
#
ike profile 1
keychain 1
local-identity address 100.1.1.1
match remote identity address 100.1.1.2 255.255.255.255
proposal 1
#
ike proposal 1
#
ike keychain 1
pre-shared-key address 100.1.1.2 255.255.255.255 key cipher $c$3$a6koxtNTlbJO2YI4f1peqpunVoLiFSqVWQ==
#
return
<R2>display current-configuration
#
version 7.1.064, Release 0821P11
#
sysname R2
#
system-working-mode standard
xbar load-single
password-recovery enable
lpu-type f-series
#
vlan 1
#
interface Serial1/0
#
interface Serial2/0
#
interface Serial3/0
#
interface Serial4/0
#
interface NULL0
#
interface GigabitEthernet0/0
port link-mode route
combo enable copper
ip address 100.1.1.2 255.255.255.0
nat outbound name ipsec_ip_nonat
ipsec apply policy ipsec_ip
#
interface GigabitEthernet0/1
port link-mode route
combo enable copper
ip address 192.168.20.254 255.255.255.0
#
interface GigabitEthernet0/2
port link-mode route
combo enable copper
#
interface GigabitEthernet5/0
port link-mode route
combo enable copper
#
interface GigabitEthernet5/1
port link-mode route
combo enable copper
#
interface GigabitEthernet6/0
port link-mode route
combo enable copper
#
interface GigabitEthernet6/1
port link-mode route
combo enable copper
#
scheduler logfile size 16
#
line class aux
user-role network-operator
#
line class console
user-role network-admin
#
line class tty
user-role network-operator
#
line class vty
user-role network-operator
#
line aux 0
user-role network-operator
#
line con 0
user-role network-admin
#
line vty 0 63
user-role network-operator
#
ip route-static 192.168.10.0 24 100.1.1.1
#
acl advanced name ipsec_ip
rule 0 permit ip source 192.168.20.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
#
acl advanced name ipsec_ip_nonat
rule 0 deny ip source 192.168.20.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
#
domain system
#
domain default enable system
#
role name level-0
description Predefined level-0 role
#
role name level-1
description Predefined level-1 role
#
role name level-2
description Predefined level-2 role
#
role name level-3
description Predefined level-3 role
#
role name level-4
description Predefined level-4 role
#
role name level-5
description Predefined level-5 role
#
role name level-6
description Predefined level-6 role
#
role name level-7
description Predefined level-7 role
#
role name level-8
description Predefined level-8 role
#
role name level-9
description Predefined level-9 role
#
role name level-10
description Predefined level-10 role
#
role name level-11
description Predefined level-11 role
#
role name level-12
description Predefined level-12 role
#
role name level-13
description Predefined level-13 role
#
role name level-14
description Predefined level-14 role
#
user-group system
#
ipsec transform-set 1
esp encryption-algorithm aes-cbc-128
esp authentication-algorithm sha1
#
ipsec policy ipsec_ip 1 isakmp
transform-set 1
security acl name ipsec_ip
local-address 100.1.1.2
remote-address 100.1.1.1
ike-profile 1
#
ike profile 1
keychain 1
local-identity address 100.1.1.2
match remote identity address 100.1.1.1 255.255.255.255
proposal 1
#
ike proposal 1
#
ike keychain 1
pre-shared-key address 100.1.1.1 255.255.255.255 key cipher $c$3$g1KcjNgswvhbd+WAqzeWWHLy2zR6KigPlQ==
#
return
- 2022-01-04回答
- 评论(4)
- 举报
-
(0)

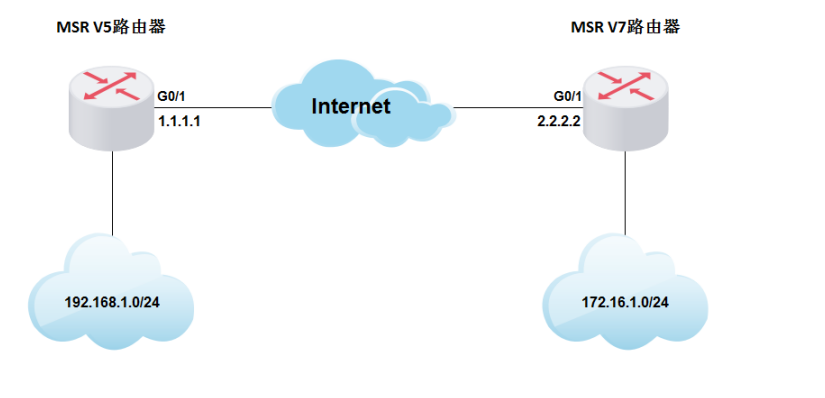
您好,参考这个案例
MSR V5平台和MSR V7平台路由器IPSec VPN对接典型配置(主模式)
1 配置需求或说明
1.1 适用产品系列
本案例提到的MSR V5平台路由器是指Comware V5 软件平台MSR WiNet系列路由器,如MSR830-WiNet 、MSR 830-10-WiNet 、MSR 930-WiNet 、MSR 930-10-WiNet 、MSR 930-WiNet-W 、MSR 2600-10-WiNet等
本案例提到的MSR V7平台路由器是指Comware V7平台的MSR830-WiNet系列路由器,如MSR830-10BEI-WiNet 、MSR830-6EI-WiNet 、MSR830-5BEI-WiNet 、MSR830-6BHI-WiNet 、MSR830-10BHI-WiNet等
1.2 配置需求及实现的效果
MSR V5路由器外网口G0/1的地址为1.1.1.1(模拟运营商公网固定地址环境),MSR V7路由器外网口G0/1的地址为2.2.2.2(模拟运营商公网固定地址环境),两个路由器外网口地址之间路由可达可以互相ping通。要实现对MSR V5所在的内网(192.168.1.0/24)与MSR V7路由器所在的内网(172.16.1.0/24)之间的数据流进行安全保护,实现两端内网终端通过IPsec VPN 隧道进行互访。
2 组网图
3 配置步骤
3.1 配置路由器基本上网
#路由器基本上网配置省略,MSR V5路由器的上网具体设置步骤请参考“2.1.2 路由器外网使用固定IP地址上网配置方法”章节中“MSR830[930][2600]系列路由器基本上网(静态IP)命令行配置(V5)”案例,MSR V7路由器的上网具体设置步骤请参考“2.1.2 路由器外网使用固定IP地址上网配置方法”章节中“MSR830-WiNet系列路由器基本上网(静态IP)命令行配置(V7)”案例
3.2 设置MSR V5路由器IPSEC VPN
# 配置一个访问控制列表3000,定义由子网192.168.1.0/24去子网172.16.1.0/24的数据流。
<H3C>system-view
[H3C]acl number 3000
[H3C-acl-adv-3000]rule 0 permit ip source 192.168.1.0 0.0.0.255 destination 172.16.1.0 0.0.0.255
[H3C-acl-adv-3000]quit
#配置公网口NAT要关联的ACl 3001,作用是把IPSec感兴趣流从NAT转换的数据流deny掉,防止IPSec数据流被NAT优先转换
[H3C]acl number 3001
[H3C-acl-adv-3001]rule 0 deny ip source 192.168.1.0 0.0.0.255 destination 172.16.1.0 0.0.0.255
[H3C-acl-adv-3001]rule 1 permit ip
[H3C-acl-adv-3001]quit
# 创建一条IKE提议1,指定IKE提议使用的认证算法为MD5,加密算法为3des-cbc
[H3C]ike proposal 1
[H3C-ike-proposal-1]authentication-algorithm md5
[H3C-ike-proposal-1]encryption-algorithm 3des-cbc
[H3C-ike-proposal-1]quit
# 配置IPSec安全提议v5,配置ESP协议采用的加密算法为3des,采用的认证算法md5
[H3C]ipsec transform-set v5
[H3C-ipsec-transform-set-v5]encapsulation-mode tunnel
[H3C-ipsec-transform-set-v5]transform esp
[H3C-ipsec-transform-set-v5]esp encryption-algorithm 3des
[H3C-ipsec-transform-set-v5]esp authentication-algorithm md5
[H3C-ipsec-transform-set-v5]quit
# 创建IKE对等体v5,预共享密钥为123456,引用之前创建的IKE安全提议1,配置对端地址为对端公网接口地址2.2.2.2,本地地址为本端的公网接口地址1.1.1.1
[H3C]ike peer v5
[H3C-ike-peer-v5]pre-shared-key 123456
[H3C-ike-peer-v5]proposal 1
[H3C-ike-peer-v5]remote-address 1.1.1.1
[H3C-ike-peer-v5]local-address 2.2.2.2
[H3C-ike-peer-v5]quit
# 创建一条IPSec安全策略v5,协商方式为isakmp。引用之前创建的感兴趣数据流ACL3000,引用之前创建的对等体v5,引用之前的IPSec安全提议v5
[H3C]ipsec policy v5 1 isakmp
[H3C-ipsec-policy-isakmp-v5-1]security acl 3000
[H3C-ipsec-policy-isakmp-v5-1]ike-peer v5
[H3C-ipsec-policy-isakmp-v5-1]transform-set v5
[H3C-ipsec-policy-isakmp-v5-1]quit
#设置外网口做NAT转换的时候关联ACL 3001 (如果之前已经在外网口配置了 nat outbound,需要先undo掉),并将IPSec安全策略v5应用在外网接口
[H3C]interface GigabitEthernet 0/1
[H3C-GigabitEthernet0/1]undo natbound
[H3C-GigabitEthernet0/1]nat outbound 3001
[H3C-GigabitEthernet0/1]ipsec policy v5
[H3C-GigabitEthernet0/1]quit
3.3 设置MSR V7路由器IPSEC VPN
# 配置一个访问控制列表,定义由子网172.16.1.0/24去子网192.168.1.0/24的数据流。
<H3C>system-view
[H3C]acl advanced 3000
[H3C-acl-ipv4-adv-3000]rule 0 permit ip source 172.16.1.0 0.0.0.255 destination 192.168.1.0 0.0.0.255
[H3C-acl-ipv4-adv-3000]quit
#配置公网口NAT要关联的ACl 3001,作用是把IPSec感兴趣流从NAT转换的数据流deny掉,防止IPSec数据流被NAT优先转换
[H3C]acl advanced 3001
[H3C-acl-ipv4-adv-3001]rule 0 deny ip source 172.16.1.0 0.0.0.255 destination 192.168.1.0 0.0.0.255
[H3C-acl-ipv4-adv-3001]rule 1 permit ip
[H3C-acl-adv-3001]quit
# 创建一条IKE提议1,指定IKE提议使用的认证算法为MD5,加密算法为3des-cbc
[H3C]ike proposal 1
[H3C-ike-proposal-1]authentication-algorithm md5
[H3C-ike-proposal-1]encryption-algorithm 3des-cbc
[H3C-ike-proposal-1]quit
[H3C]ike keychain v7
#配置对端IP地址为1.1.1.1,使用的预共享密钥为明文123456
[H3C-ike-keychain-v7]pre-shared-key address 1.1.1.1 255.255.255.0 key simple 123456
[H3C-ike-keychain-v7]quit
# 创建并配置IKE profile,名称为v7,引用上面配置的keychain v7,配置本地地址为本端的公网接口地址2.2.2.2,对端地址为对端公网接口地址1.1.1.1,引用之前配置IKE提议1
[H3C]ike profile v7
[H3C-ike-profile-v7]keychain v7
[H3C-ike-profile-v7]local-identity address 2.2.2.2
[H3C-ike-profile-v7]match remote identity address 1.1.1.1 255.255.255.0
[H3C-ike-profile-v7]proposal 1
[H3C-ike-profile-v7]quit
# 配置IPsec安全提议v7,ESP协议采用的加密算法为3des-cbc,认证算法为md5
[H3C]ipsec transform-set v7
[H3C-ipsec-transform-set-v7]encapsulation-mode tunnel
[H3C-ipsec-transform-set-v7]esp encryption-algorithm 3des-cbc
[H3C-ipsec-transform-set-v7]esp authentication-algorithm md5
[H3C-ipsec-transform-set-v5]quit
#创建IPsec安全策略,名称为v7,序列号为1,设置对端地址为对端公网地址1.1.1.1,引用之前创建的ACL3000,引用之前创建的IKE profile v7,引用之前的IPSec安全提议v7
[H3C]ipsec policy v7 1 isakmp
[H3C-ipsec-policy-isakmp-v7-1]remote-address 1.1.1.1
[H3C-ipsec-policy-isakmp-v7-1]security acl 3000
[H3C-ipsec-policy-isakmp-v7-1]transform-set v7
[H3C-ipsec-policy-isakmp-v7-1]ike-profile v7
[H3C-ipsec-policy-isakmp-v7-1]quit
#设置外网口做NAT转换的时候关联ACL 3001 (如果之前已经在外网口配置了 nat outbound,需要先undo掉),并将IPSec安全策略v7应用在外网接口
[H3C]interface GigabitEthernet 0/1
[H3C-GigabitEthernet0/1]undo nat outbound
[H3C-GigabitEthernet0/1]nat outbound 3001
[H3C-GigabitEthernet0/1]ipsec apply policy v7
[H3C-GigabitEthernet0/1]quit
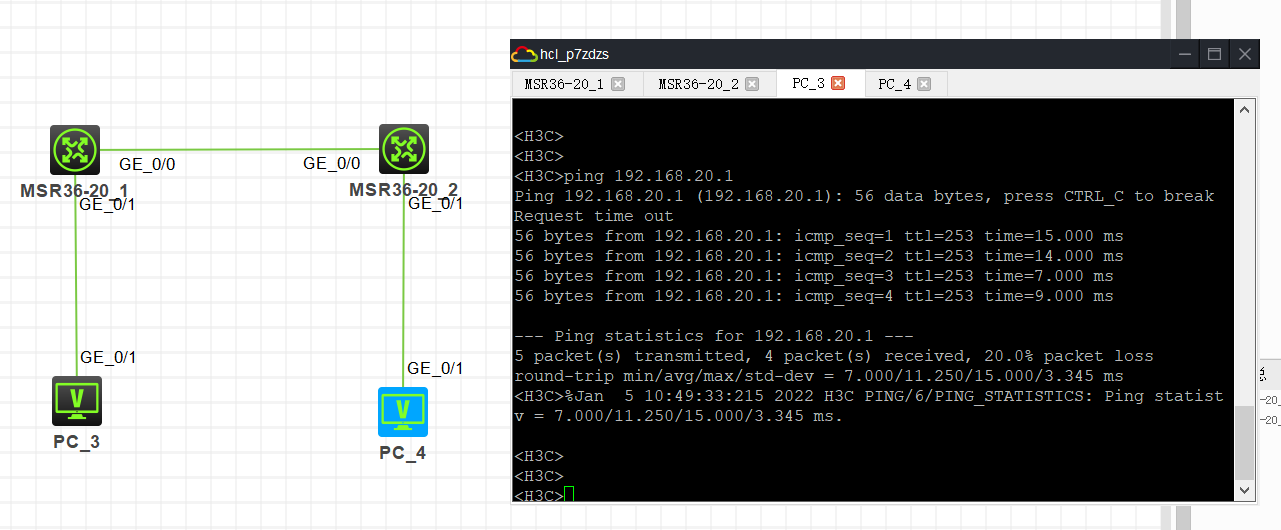
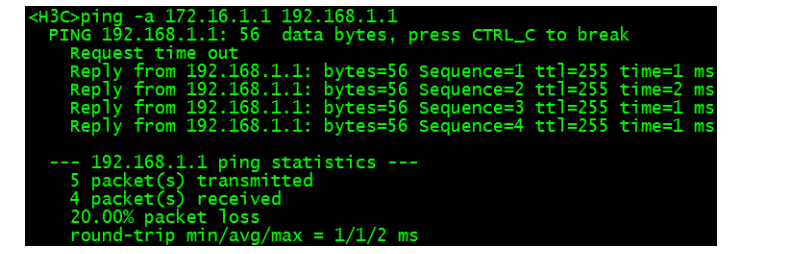
3.4 验证配置结果
#在MSR V7路由器上带源ping MSR V5路由器内网网关地址
- 2022-01-04回答
- 评论(1)
- 举报
-
(0)
第一阶段ike sa还是无法起来,开启debug ike 也没看到相关日志,就好像没任何流量一样,手动rest ike sa也试过不行
第一阶段ike sa还是无法起来,开启debug ike 也没看到相关日志,就好像没任何流量一样,手动rest ike sa也试过不行
编辑答案


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明





是写错了,实际是策略名称是ipsec