H3C SecPath F1000 一个接口配置多个IPsec
- 1关注
- 2收藏,4530浏览
问题描述:
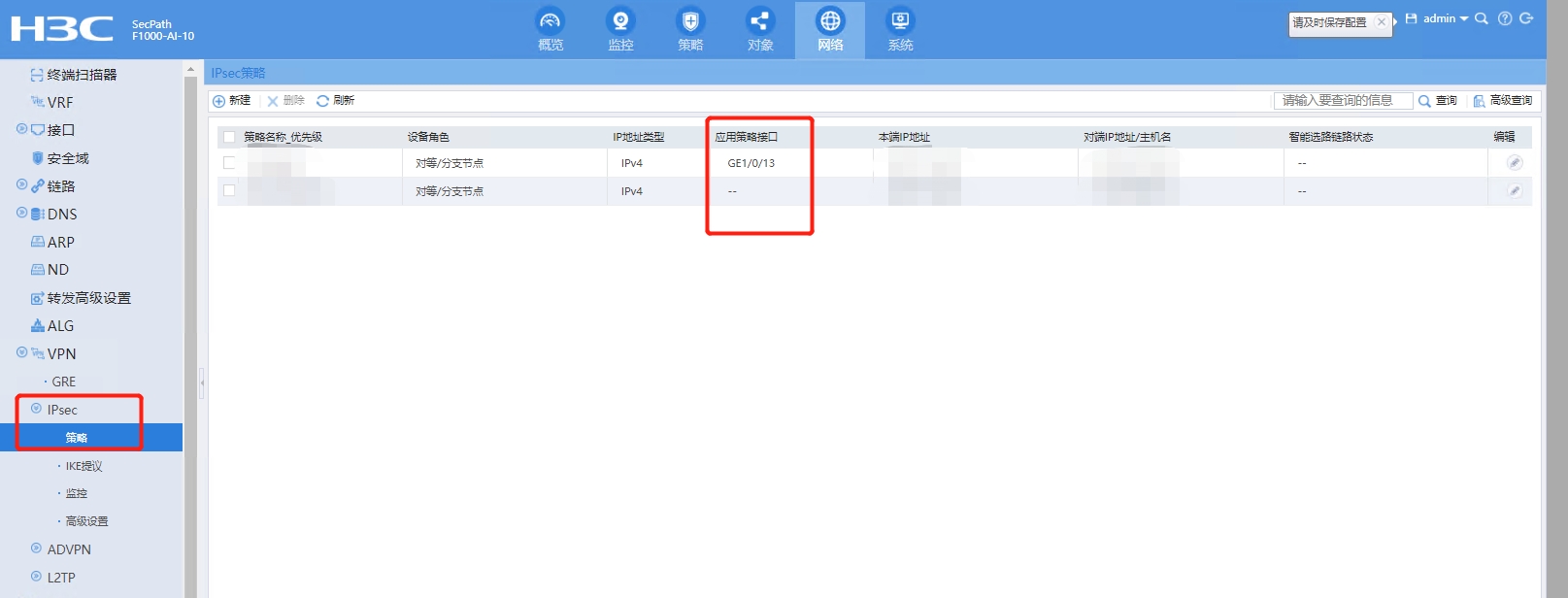
我在想配置IPsec去连和多个地区相连,配置时选择了外网接入端口,配置第二个时也选了同个出去的端口,但第一个却断开了连接。是一个端口不允许配置多个IPsec吗?还是我这台防火墙不支持呢,或者说有其他方法可以实现?求大佬!!
组网及组网描述:
- 2022-10-21提问
- 举报
-
(0)


您好,一个接口只能调用一个ipsec policy
如果一个接口需要对接多个不同dipsec邻居通过policy优先级区分即可。
参考案例https://zhiliao.h3c.com/Theme/details/22400
F10X0双链路备份IPSEC典型配置案例
- 2022-10-21回答
- 评论(0)
- 举报
-
(1)
暂无评论

您好,请知:
可以使用一个IPSEC策略,多个id。
然后在接口调用一个IPSEC策略即可,因为一个接口只能调用一个IPSEC策略。
可参考如下配置案例:
防火墙A和防火墙B分别有两个公网出口,需要建立两条负载分担互为主备的IPSEC隧道,使用IPSEC保护两边私网地址的互通,要求实现数据在不同的接口间平滑切换,使用IKE建立IPSEC SA,配置共享源接口IPSEC安全策略。
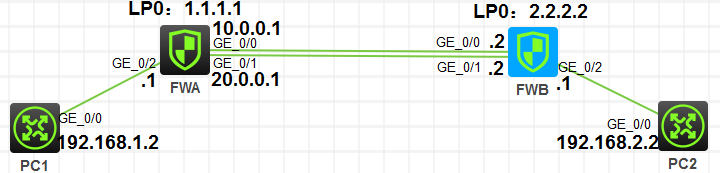
1.首先配置路由,使本地的Loopback口和两个公网地址能和对端的两个公网口和Loopback口路由互通。
2.配置域间策略
#
security-zone name Trust
import interface GigabitEthernet1/0/2
#
security-zone name Untrust
import interface GigabitEthernet1/0/0
import interface GigabitEthernet1/0/1
import interface LoopBack0
#
zone-pair security source Any destination Any
packet-filter 3000
#
acl advanced 3000
rule 5 permit ip
#
3.防火墙A关于IPSEC的主要配置:
//设置本地环回口
interface LoopBack0
ip address 1.1.1.1 255.255.255.255
#
//配置IPSEC感兴趣流,匹配本端访问对端
acl advanced 3000
rule 0 permit ip source 192.168.1.0 0.0.0.255 destination 192.168.2.0 0.0.0.255
#
//配置IPSEC安全提议
ipsec transform-set test1
esp encryption-algorithm 3des-cbc
esp authentication-algorithm md5
#
//配置ike profile,指定本地和对端地址,引用keychain
ike profile 1
keychain A
local-identity address 1.1.1.1
match remote identity address 2.2.2.2 255.255.255.255
#
//配置ike keychain,设置预共享密钥
ike keychain A
pre-shared-key address 2.2.2.2 255.255.255.255 key cipher $c$3$8rjR9bl0S4EUcPPzs8nK9ZAj0nd+fNFkgQ==
#
//配置IPSEC策略,指定感兴趣流、IPSEC安全提议、远端地址可IKE协商的profile
ipsec policy yewu 1 isakmp
transform-set test1
security acl 3000
remote-address 2.2.2.2
ike-profile 1
#
//在两个公网出来引用IPSEC策略
interface GigabitEthernet1/0/0
ip address 10.0.0.1 255.255.255.0
ipsec apply policy yewu
#
interface GigabitEthernet1/0/1
ip address 20.0.0.1 255.255.255.0
ipsec apply policy yewu
#
// 配置共享源接口IPsec安全策略
ipsec policy yewu local-address LoopBack0
#
防火墙B关于IPSEC的主要配置:
#
ospf 1
area 0.0.0.0
network 2.2.2.2 0.0.0.0
network 10.0.0.0 0.0.0.255
network 20.0.0.0 0.0.0.255
#
interface LoopBack0
ip address 2.2.2.2 255.255.255.255
#
interface GigabitEthernet1/0/0
ip address 10.0.0.2 255.255.255.0
ipsec apply policy test
#
interface GigabitEthernet1/0/1
ip address 20.0.0.2 255.255.255.0
ipsec apply policy test
#
interface GigabitEthernet1/0/2
ip address 192.168.2.1 255.255.255.0
#
security-zone name Trust
import interface GigabitEthernet1/0/2
#
security-zone name Untrust
import interface GigabitEthernet1/0/0
import interface GigabitEthernet1/0/1
import interface LoopBack0
#
zone-pair security source Any destination Any
packet-filter 3000
#
ip route-static 0.0.0.0 0 10.0.0.1
ip route-static 0.0.0.0 0 20.0.0.1
#
acl advanced 3000
rule 5 permit ip
#
acl advanced 3001
rule 0 permit ip source 192.168.2.0 0.0.0.255 destination 192.168.1.0 0.0.0.255
#
ipsec transform-set test
esp encryption-algorithm 3des-cbc
esp authentication-algorithm md5
#
ipsec policy test 1 isakmp
transform-set test
security acl 3001
remote-address 1.1.1.1
ike-profile test
#
ipsec policy test local-address LoopBack0
#
ike profile test
keychain test
local-identity address 2.2.2.2
match remote identity address 1.1.1.1 255.255.255.255
#
ike keychain test
pre-shared-key address 1.1.1.1 255.255.255.255 key cipher $c$3$728nyqc1kO4fGgsRZ5bzuEhoOnPIIlzeAw==
#
4.IPSEC隧道建立情况
防火墙A上面查看:
<FWA>dis ike sa
Connection-ID Remote Flag DOI
------------------------------------------------------------------
1 2.2.2.2 RD IPsec
Flags:
RD--READY RL--REPLACED FD-FADING RK-REKEY
<FWA>dis ipsec sa
-------------------------------
Interface: LoopBack0
-------------------------------
-----------------------------
IPsec policy: test
Sequence number: 1
Mode: ISAKMP
-----------------------------
Tunnel id: 0
Encapsulation mode: tunnel
Perfect Forward Secrecy:
Inside VPN:
Extended Sequence Numbers enable: N
Traffic Flow Confidentiality enable: N
Path MTU: 1480
Tunnel:
local address: 1.1.1.1
remote address: 2.2.2.2
Flow:
sour addr: 192.168.1.0/255.255.255.0 port: 0 protocol: ip
dest addr: 192.168.2.0/255.255.255.0 port: 0 protocol: ip
[Inbound ESP SAs]
SPI: 976657142 (0x3a369af6)
Connection ID: 4294967296
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-MD5
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843166/1262
Max received sequence-number: 394
Anti-replay check enable: Y
Anti-replay window size: 64
UDP encapsulation used for NAT traversal: N
Status: Active
[Outbound ESP SAs]
SPI: 1402450213 (0x5397b125)
Connection ID: 4294967297
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-MD5
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843166/1262
Max sent sequence-number: 394
UDP encapsulation used for NAT traversal: N
Status: Active
防火墙B上面查看:
<FWB>dis ike sa
Connection-ID Remote Flag DOI
------------------------------------------------------------------
1 1.1.1.1 RD IPsec
Flags:
RD--READY RL--REPLACED FD-FADING RK-REKEY
<FWB>dis ipsec sa
-------------------------------
Interface: LoopBack0
-------------------------------
-----------------------------
IPsec policy: test
Sequence number: 1
Mode: ISAKMP
-----------------------------
Tunnel id: 0
Encapsulation mode: tunnel
Perfect Forward Secrecy:
Inside VPN:
Extended Sequence Numbers enable: N
Traffic Flow Confidentiality enable: N
Path MTU: 1480
Tunnel:
local address: 2.2.2.2
remote address: 1.1.1.1
Flow:
sour addr: 192.168.2.0/255.255.255.0 port: 0 protocol: ip
dest addr: 192.168.1.0/255.255.255.0 port: 0 protocol: ip
[Inbound ESP SAs]
SPI: 1402450213 (0x5397b125)
Connection ID: 4294967296
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-MD5
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843166/908
Max received sequence-number: 394
Anti-replay check enable: Y
Anti-replay window size: 64
UDP encapsulation used for NAT traversal: N
Status: Active
[Outbound ESP SAs]
SPI: 976657142 (0x3a369af6)
Connection ID: 4294967297
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-MD5
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843166/908
Max sent sequence-number: 394
UDP encapsulation used for NAT traversal: N
Status: Active
-----------------------------
IPsec policy: test
Sequence number: 1
Mode: ISAKMP
-----------------------------
Tunnel id: 0
Encapsulation mode: tunnel
Perfect Forward Secrecy:
Inside VPN:
Extended Sequence Numbers enable: N
Traffic Flow Confidentiality enable: N
Path MTU: 1480
Tunnel:
local address: 2.2.2.2
remote address: 1.1.1.1
Flow:
sour addr: 192.168.2.0/255.255.255.0 port: 0 protocol: ip
dest addr: 192.168.1.0/255.255.255.0 port: 0 protocol: ip
[Inbound ESP SAs]
SPI: 3700197029 (0xdc8c86a5)
Connection ID: 4294967298
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-MD5
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843200/3587
Max received sequence-number: 0
Anti-replay check enable: Y
Anti-replay window size: 64
UDP encapsulation used for NAT traversal: N
Status: Active
[Outbound ESP SAs]
SPI: 235320017 (0x0e06b2d1)
Connection ID: 4294967299
Transform set: ESP-ENCRYPT-3DES-CBC ESP-AUTH-MD5
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1843200/3587
Max sent sequence-number: 0
UDP encapsulation used for NAT traversal: N
Status: Active
5.双链路负载分担平滑切换测试:
<FWA>ping -a 192.168.1.1 -c 1000 192.168.2.2
Ping 192.168.2.2 (192.168.2.2) from 192.168.1.1: 56 data bytes, press CTRL_C to break
56 bytes from 192.168.2.2: icmp_seq=10 ttl=254 time=3.000 ms
56 56 bytes from 192.168.2.2: icmp_seq=146 ttl=254 time=1.000 ms
%Dec 19 19:48:08:227 2017 H3C IFNET/3/PHY_UPDOWN: -COntext=1; Physical state on the interface GigabitEthernet1/0/1 changed to down.
%Dec 19 19:48:08:228 2017 H3C IFNET/5/LINK_UPDOWN: -COntext=1; Line protocol state on the interface GigabitEthernet1/0/1 changed to down.
%Dec 19 19:48:08:230 2017 H3C OSPF/5/OSPF_NBR_CHG: -COntext=1; OSPF 1 Neighbor 20.0.0.2(GigabitEthernet1/0/1) changed from INIT to DOWN.
56 bytes from 192.168.2.2: icmp_seq=147 ttl=254 time=1.000 ms
56 bytes from 192.168.2.2: icmp_seq=157 ttl=254 time=3.000 ms
56 bytes from 192.168.2.2: icmp_seq=158 ttl=254 time=3.000 ms
56 bytes from 192.168.2.2: icmp_seq=159 ttl=254 time=1.000 ms
56 bytes from 192.168.2.2: icmp_
--- Ping statistics for 192.168.2.2 ---
161 packet(s) transmitted, 161 packet(s) received, 0.0% packet loss
round-trip min/avg/max/std-dev = 0.000/1.981/8.000/1.302 ms
<H3C>%Dec 19 19:48:11:018 2017 H3C PING/6/PING_STATISTICS: -COntext=1; Ping statistics for 192.168.2.2: 161 packet(s) transmitted, 161 packet(s) received, 0.0% packet loss, round-trip min/avg/max/std-dev = 0.000/1.981/8.000/1.302 ms.
为了提高网络的可靠性,通常核心设备到ISP(Internet Service Provider,互联网服务提供商)都会有两条出口链路,它们互为备份或者为负载分担的关系。由于在不同的接口上应用安全策略时,各个接口将分别协商生成IPsec SA。因此,则在主备链路切换时,接口状态的变化会触发重新进行IKE协商,从而导致数据流的暂时中断。这种情况下,通过将一个IPsec安全策略与一个源接口绑定,使之成为共享源接口IPsec安全策略,可以实现主备链路切换时受IPsec保护的业务流量不中断。
对于本配置,有以下配置限制和注意事项:
· 只有IKE协商方式的IPsec安全策略才能配置为IPsec共享源接口安全策略。
· 一个IPsec安全策略只能与一个源接口绑定。
· 一个源接口可以同时与多个IPsec安全策略绑定。
· 删除与共享源接口IPsec安全策略绑定的共享源接口时,将使得该共享源接口IPsec安全策略恢复为普通IPsec安全策略。
· 若一个IPsec安全策略为共享源接口IPsec安全策略,但该IPsec安全策略中未指定隧道本端地址,则IKE将使用共享源接口地址作为IPsec隧道的本端地址进行IKE协商;如果共享源接口IPsec安全策略中指定了隧道本端地址,则将使用指定的隧道本端地址进行IKE协商。
- 2022-10-22回答
- 评论(0)
- 举报
-
(1)
暂无评论
编辑答案


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明


暂无评论