华三防火墙+SNMP为什么没有配置团体字符串
- 0关注
- 1收藏,4461浏览
问题描述:
工程师 您好:
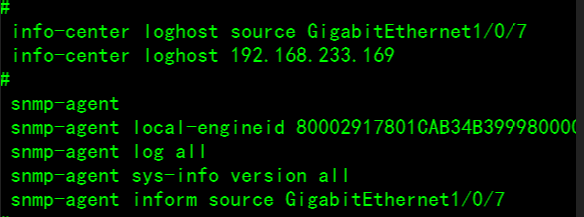
麻烦解答下上面的图中的配置,
我配置了一个snmp服务器,将华三防火墙上的信息发送到snmp服务器上,配置如上
为什么这个snmp里面没有团体字符串了 ?
组网及组网描述:
- 2018-10-08提问
- 举报
-
(0)
最佳答案

设置团体字的关键字是community,完整命令是 ,在系统试图下
[H3C] snmp-agent community read simple xxxx
- 2018-10-08回答
- 评论(3)
- 举报
-
(0)
您好, 华三现场工程师在配置里面没有配置读团体字符,但是现在业务是正常的,我想问下,是不是只配置上面截图中的命令就好了 ?
没有默认的团体字哦 , 配置如下: # version 7.1.064, Release 9502P14 # sysname EnvisionWF-271-XCLT-Zone1&2 # context Admin id 1 # irf mac-address persistent timer irf auto-update enable undo irf link-delay irf member 1 priority 1 # nat address-group 2 name "FEP1 to AGC" address 192.168.5.251 192.168.5.251 # nat address-group 3 name "FEP2 to AGC" address 192.168.5.253 192.168.5.253 # nat address-group 4 name "FEP1 to YangDong" address 172.20.1.251 172.20.1.251 # nat address-group 5 name "FEP2 to YuanDong" address 172.20.1.253 172.20.1.253 # password-recovery enable # vlan 1 # object-group ip address AGC security-zone AGC 0 network host address 192.168.5.241 # object-group ip address FEP1 security-zone Zone1 0 network host address 192.168.233.144 # object-group ip address FEP2 security-zone Zone1 0 network host address 192.168.233.148 # object-group ip address internet1 security-zone Zone1 0 network subnet 192.168.233.128 255.255.255.224 # object-group ip address internet2 security-zone Zone2 0 network subnet 192.168.233.160 255.255.255.224 # object-group ip address MON security-zone Zone1 0 network host address 192.168.233.140 # object-group ip address Permin security-zone Trust 0 network subnet 192.168.0.0 255.255.255.0 # object-group ip address YuanDong1 security-zone YuanDong 0 network host address 172.20.1.223 # object-group ip address YuanDong2 security-zone YuanDong 0 network host address 172.20.1.233 # object-group service AWS 0 service tcp destination range 2451 2458 10 service tcp destination range 2461 2468 # object-group service BUFF 0 service tcp destination range 2431 2445 # object-group service TCP_2404 0 service tcp destination eq 2404 # object-group service TCP_2404-2410 0 service tcp destination range 2404 2410 # interface NULL0 # interface GigabitEthernet1/0/0 port link-mode route combo enable copper ip address 192.168.0.1 255.255.255.0 # interface GigabitEthernet1/0/1 port link-mode route combo enable fiber ip address 192.168.5.251 255.255.255.0 ip address 192.168.5.253 255.255.255.0 sub nat outbound 3113 address-group 3 port-preserved nat outbound 3112 address-group 2 port-preserved nat server protocol tcp global 192.168.5.251 2404 inside 192.168.233.144 2404 nat server protocol tcp global 192.168.5.253 2404 inside 192.168.233.148 2404 # interface GigabitEthernet1/0/2 port link-mode route ip address 192.168.1.1 255.255.255.0 # interface GigabitEthernet1/0/3 port link-mode route ip address 172.20.1.251 255.255.255.0 ip address 172.20.1.253 255.255.255.0 sub nat outbound 3115 address-group 5 port-preserved nat outbound 3114 address-group 4 port-preserved nat server protocol tcp global 172.20.1.251 2404 inside 192.168.233.144 2404 nat server protocol tcp global 172.20.1.253 2404 inside 192.168.233.148 2404 # interface GigabitEthernet1/0/4 port link-mode route # interface GigabitEthernet1/0/5 port link-mode route # interface GigabitEthernet1/0/6 port link-mode route ip address 192.168.233.129 255.255.255.224 # interface GigabitEthernet1/0/7 port link-mode route ip address 192.168.233.161 255.255.255.224 nat outbound 3111 port-preserved # interface GigabitEthernet1/0/8 port link-mode route # interface GigabitEthernet1/0/9 port link-mode route # interface GigabitEthernet1/0/10 port link-mode route # interface GigabitEthernet1/0/11 port link-mode route # security-zone name Local # security-zone name Trust # security-zone name DMZ # security-zone name Untrust # security-zone name Management import interface GigabitEthernet1/0/0 import interface GigabitEthernet1/0/2 # security-zone name AGC import interface GigabitEthernet1/0/1 # security-zone name YuanDong import interface GigabitEthernet1/0/3 # security-zone name Zone1 import interface GigabitEthernet1/0/6 # security-zone name Zone2 import interface GigabitEthernet1/0/7 # scheduler logfile size 16 # line class aux user-role network-operator # line class console authentication-mode scheme user-role network-admin # line class vty user-role network-operator # line aux 0 user-role network-admin # line con 0 user-role network-admin # line vty 0 63 authentication-mode scheme user-role network-admin # info-center loghost source GigabitEthernet1/0/7 info-center loghost 192.168.233.169 # snmp-agent snmp-agent local-engineid 80002917801CAB34B3999800000001 snmp-agent log all snmp-agent sys-info version all snmp-agent inform source GigabitEthernet1/0/7 # ssh server enable # acl advanced 3111 rule 0 permit ip source 192.168.233.128 0.0.0.31 destination 192.168.233.160 0.0.0.31 logging counting # acl advanced 3112 rule 0 permit ip source 192.168.233.144 0 destination 192.168.5.241 0 logging counting # acl advanced 3113 rule 0 permit ip source 192.168.233.148 0 destination 192.168.5.241 0 logging counting # acl advanced 3114 rule 0 permit ip source 192.168.233.144 0 destination 172.20.1.0 0.0.0.255 logging counting # acl advanced 3115 rule 0 permit ip source 192.168.233.148 0 destination 172.20.1.0 0.0.0.255 logging counting # domain system # aaa session-limit ftp 16 aaa session-limit telnet 16 aaa session-limit ssh 16 domain default enable system # role name level-0 description Predefined level-0 role # role name level-1 description Predefined level-1 role # role name level-2 description Predefined level-2 role # role name level-3 description Predefined level-3 role # role name level-4 description Predefined level-4 role # role name level-5 description Predefined level-5 role # role name level-6 description Predefined level-6 role # role name level-7 description Predefined level-7 role # role name level-8 description Predefined level-8 role # role name level-9 description Predefined level-9 role # role name level-10 description Predefined level-10 role # role name level-11 description Predefined level-11 role # role name level-12 description Predefined level-12 role # role name level-13 description Predefined level-13 role # role name level-14 description Predefined level-14 role # user-group system identity-member user accenture # local-user accenture class manage password hash $h$6$DkhDCTM3RYavMYHe$d+pz+Ex/uIINk7VKvUGpsWi4SH3bsGg3PAiY6JkrqqYirGLLaEefZ8085SBkRWqQx/YAFJNzmAM2hnUK3f2a+w== service-type ssh terminal http https authorization-attribute user-role level-3 authorization-attribute user-role network-admin authorization-attribute user-role network-operator # local-user admin class manage password hash $h$6$7IGhhyoWzvT0z4r5$tPhjs16TH+Eu8HhM3bmKKG1jzRUIo8lsGun2T/hLNOIhOabqG+GfPw8KJE0g0vLXa6G9NaerJ2h2fZOs0pP6qg== service-type ssh terminal https authorization-attribute user-role level-3 authorization-attribute user-role network-admin authorization-attribute user-role network-operator # ip https enable webui log enable # uapp-control # security-policy ip rule 0 name "Zone1 to Zone2" action pass counting enable source-zone Zone1 destination-zone Zone2 source-ip internet1 destination-ip internet2 service TCP_2404-2410 service AWS service BUFF service ssh service ping rule 1 name "Zone2 to Zone1" action pass counting enable source-zone Zone2 destination-zone Zone1 source-ip internet2 destination-ip internet1 service TCP_2404-2410 service ssh service ping rule 2 name "Zone2 to Zone1-1" action pass counting enable source-zone Zone2 destination-zone Zone1 source-ip internet2 destination-ip MON service ntp service ping rule 3 name "FEP to AGc" action pass counting enable source-zone Zone1 destination-zone AGC source-ip FEP1 source-ip FEP2 destination-ip AGC service TCP_2404 service ping rule 4 name "AGC to FEP" action pass counting enable source-zone AGC destination-zone Zone1 source-ip AGC destination-ip FEP1 destination-ip FEP2 service TCP_2404 service ping rule 5 name "FEP to YuanDong" action pass counting enable source-zone Zone1 destination-zone YuanDong source-ip FEP1 source-ip FEP2 destination-ip YuanDong1 destination-ip YuanDong2 service TCP_2404 service ping rule 6 name "YuanDong to FEP" action pass counting enable source-zone YuanDong destination-zone Zone1 source-ip YuanDong1 source-ip YuanDong2 destination-ip FEP1 destination-ip FEP2 service TCP_2404 service ping rule 7 name localout action pass counting enable source-zone Local destination-zone Zone1 destination-zone Zone2 destination-zone AGC destination-zone YuanDong rule 8 name localin action pass counting enable source-zone Zone1 source-zone Zone2 source-zone AGC source-zone YuanDong # return

配置SNMPv1/v2c版本基本参数
为了安全起见,只有具有network-admin、context-admin或者level-15用户角色的用户登录设备后才能创建SNMP团体、用户或组。其它角色的用户,即使授权了SNMP特性或相应命令的操作权限,也不能执行相应命令。
表1-1 配置SNMPv1/v2c版本基本参数
|
操作 |
命令 |
说明 | ||
|
进入系统视图 |
system-view |
- |
||
|
(可选)启动SNMP Agent服务 |
snmp-agent |
缺省情况下,SNMP Agent服务处于关闭状态 执行除snmp-agent calculate-password外任何以snmp-agent开头的命令,都可以启动SNMP Agent服务 |
||
|
(可选)配置设备的维护联系信息 |
snmp-agent sys-info contact sys-contact |
|||
|
(可选)配置设备的物理位置信息 |
snmp-agent sys-info location sys-location |
|||
|
配置设备支持SNMPv1/v2c版本 |
snmp-agent sys-info version { all | { v1 | v2c | v3 } *} |
缺省情况下,系统启用的SNMP版本号为“SNMPv3” |
||
|
(可选)配置本设备的SNMP引擎ID |
snmp-agent local-engineid engineid |
缺省情况下,设备引擎ID为公司的“企业号+设备信息” |
||
|
(可选)配置远端SNMP实体的引擎ID |
snmp-agent remote { ipv4-address | ipv6 ipv6-address } [ vpn-instance vpn-instance-name ] engineid engineid |
缺省情况下,不存在远端SNMP实体的引擎ID 当设备需要向目的主机(能够解析Trap和Inform报文的设备,通常为NMS)发送SNMPv3 Inform报文时,该步骤必选 |
||
|
(可选)创建或者更新MIB视图 |
snmp-agent mib-view { excluded | included } view-name oid-tree [ mask mask-value ] |
缺省情况下,存在四个MIB视图,名称均为ViewDefault: · 视图一包含MIB子树iso · 视图二不包含子树snmpUsmMIB · 视图三不包含子树snmpVacmMIB · 视图四不包含子树snmpModules.18 MIB视图是MIB的子集,由视图名和MIB子树来唯一确定一个MIB视图。视图名相同但包含的子树不同,则认为是不同的视图 |
||
|
配置访问权限 |
直接配置 |
创建SNMP团体 |
VACM方式: snmp-agent community { read | write } [ simple | cipher ] community-name [ mib-view view-name ] [ acl { ipv4-acl-number | name ipv4-acl-name } | acl ipv6 { ipv6-acl-number | name ipv6-acl-name } ] * |
二者选其一 直接配置是以SNMPv1和SNMPv2c版本的团体名进行配置 间接配置是先创建SNMP组,再向创建的组中添加的用户,用户相当于SNMPv1和SNMPv2c版本的团体名,在NMS上配置的团体名需要跟Agent上配置的用户名一致 缺省情况下,不存在任何SNMP组和SNMP团体 |
|
RBAC方式: snmp-agent community [ simple | cipher ] community-name user-role role-name [ acl { ipv4-acl-number | name ipv4-acl-name } | acl ipv6 { ipv6-acl-number | name ipv6-acl-name } ] * |
||||
|
间接配置 |
创建SNMPv1/v2c组 |
snmp-agent group { v1 | v2c } group-name [ read-view view-name ] [ write-view view-name ] [ notify-view view-name ] [ acl { ipv4-acl-number | name ipv4-acl-name } | acl ipv6 { ipv6-acl-number | name ipv6-acl-name } ] * |
||
|
创建SNMPv1/v2c用户 |
snmp-agent usm-user { v1 | v2c } user-name group-name [ acl { ipv4-acl-number | name ipv4-acl-name } | acl ipv6 { ipv6-acl-number | name ipv6-acl-name } ] * |
|||
|
(可选)创建SNMP上下文 |
snmp-agent context context-name |
缺省情况下,不存在SNMP上下文 |
||
|
(可选)创建团体名到SNMP上下文的映射 |
snmp-agent community-map community-name context context-name |
缺省情况下,不存在团体名到SNMP上下文的映射 |
||
|
(可选)配置Agent能处理的SNMP报文的最大长度 |
snmp-agent packet max-size byte-count |
缺省情况下,Agent能接收/发送的SNMP消息包长度的最大值为1500字节 |
||
|
(可选)配置设备上接收SNMP报文的端口号 |
snmp-agent port port-num |
缺省情况下,使用161号端口接收SNMP报文 | ||
- 2018-10-08回答
- 评论(1)
- 举报
-
(0)
工程师您好, 华三工程师现场配置上面的命令,信息可以上传到snmp服务器,但是不理解既然采用了snmp,为什么没有配置团体字符,不是权限的问题。请帮忙解答下,谢谢。
工程师您好, 华三工程师现场配置上面的命令,信息可以上传到snmp服务器,但是不理解既然采用了snmp,为什么没有配置团体字符,不是权限的问题。请帮忙解答下,谢谢。
编辑答案


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明


没有默认的团体字哦 , 配置如下: # version 7.1.064, Release 9502P14 # sysname EnvisionWF-271-XCLT-Zone1&2 # context Admin id 1 # irf mac-address persistent timer irf auto-update enable undo irf link-delay irf member 1 priority 1 # nat address-group 2 name "FEP1 to AGC" address 192.168.5.251 192.168.5.251 # nat address-group 3 name "FEP2 to AGC" address 192.168.5.253 192.168.5.253 # nat address-group 4 name "FEP1 to YangDong" address 172.20.1.251 172.20.1.251 # nat address-group 5 name "FEP2 to YuanDong" address 172.20.1.253 172.20.1.253 # password-recovery enable # vlan 1 # object-group ip address AGC security-zone AGC 0 network host address 192.168.5.241 # object-group ip address FEP1 security-zone Zone1 0 network host address 192.168.233.144 # object-group ip address FEP2 security-zone Zone1 0 network host address 192.168.233.148 # object-group ip address internet1 security-zone Zone1 0 network subnet 192.168.233.128 255.255.255.224 # object-group ip address internet2 security-zone Zone2 0 network subnet 192.168.233.160 255.255.255.224 # object-group ip address MON security-zone Zone1 0 network host address 192.168.233.140 # object-group ip address Permin security-zone Trust 0 network subnet 192.168.0.0 255.255.255.0 # object-group ip address YuanDong1 security-zone YuanDong 0 network host address 172.20.1.223 # object-group ip address YuanDong2 security-zone YuanDong 0 network host address 172.20.1.233 # object-group service AWS 0 service tcp destination range 2451 2458 10 service tcp destination range 2461 2468 # object-group service BUFF 0 service tcp destination range 2431 2445 # object-group service TCP_2404 0 service tcp destination eq 2404 # object-group service TCP_2404-2410 0 service tcp destination range 2404 2410 # interface NULL0 # interface GigabitEthernet1/0/0 port link-mode route combo enable copper ip address 192.168.0.1 255.255.255.0 # interface GigabitEthernet1/0/1 port link-mode route combo enable fiber ip address 192.168.5.251 255.255.255.0 ip address 192.168.5.253 255.255.255.0 sub nat outbound 3113 address-group 3 port-preserved nat outbound 3112 address-group 2 port-preserved nat server protocol tcp global 192.168.5.251 2404 inside 192.168.233.144 2404 nat server protocol tcp global 192.168.5.253 2404 inside 192.168.233.148 2404 # interface GigabitEthernet1/0/2 port link-mode route ip address 192.168.1.1 255.255.255.0 # interface GigabitEthernet1/0/3 port link-mode route ip address 172.20.1.251 255.255.255.0 ip address 172.20.1.253 255.255.255.0 sub nat outbound 3115 address-group 5 port-preserved nat outbound 3114 address-group 4 port-preserved nat server protocol tcp global 172.20.1.251 2404 inside 192.168.233.144 2404 nat server protocol tcp global 172.20.1.253 2404 inside 192.168.233.148 2404 # interface GigabitEthernet1/0/4 port link-mode route # interface GigabitEthernet1/0/5 port link-mode route # interface GigabitEthernet1/0/6 port link-mode route ip address 192.168.233.129 255.255.255.224 # interface GigabitEthernet1/0/7 port link-mode route ip address 192.168.233.161 255.255.255.224 nat outbound 3111 port-preserved # interface GigabitEthernet1/0/8 port link-mode route # interface GigabitEthernet1/0/9 port link-mode route # interface GigabitEthernet1/0/10 port link-mode route # interface GigabitEthernet1/0/11 port link-mode route # security-zone name Local # security-zone name Trust # security-zone name DMZ # security-zone name Untrust # security-zone name Management import interface GigabitEthernet1/0/0 import interface GigabitEthernet1/0/2 # security-zone name AGC import interface GigabitEthernet1/0/1 # security-zone name YuanDong import interface GigabitEthernet1/0/3 # security-zone name Zone1 import interface GigabitEthernet1/0/6 # security-zone name Zone2 import interface GigabitEthernet1/0/7 # scheduler logfile size 16 # line class aux user-role network-operator # line class console authentication-mode scheme user-role network-admin # line class vty user-role network-operator # line aux 0 user-role network-admin # line con 0 user-role network-admin # line vty 0 63 authentication-mode scheme user-role network-admin # info-center loghost source GigabitEthernet1/0/7 info-center loghost 192.168.233.169 # snmp-agent snmp-agent local-engineid 80002917801CAB34B3999800000001 snmp-agent log all snmp-agent sys-info version all snmp-agent inform source GigabitEthernet1/0/7 # ssh server enable # acl advanced 3111 rule 0 permit ip source 192.168.233.128 0.0.0.31 destination 192.168.233.160 0.0.0.31 logging counting # acl advanced 3112 rule 0 permit ip source 192.168.233.144 0 destination 192.168.5.241 0 logging counting # acl advanced 3113 rule 0 permit ip source 192.168.233.148 0 destination 192.168.5.241 0 logging counting # acl advanced 3114 rule 0 permit ip source 192.168.233.144 0 destination 172.20.1.0 0.0.0.255 logging counting # acl advanced 3115 rule 0 permit ip source 192.168.233.148 0 destination 172.20.1.0 0.0.0.255 logging counting # domain system # aaa session-limit ftp 16 aaa session-limit telnet 16 aaa session-limit ssh 16 domain default enable system # role name level-0 description Predefined level-0 role # role name level-1 description Predefined level-1 role # role name level-2 description Predefined level-2 role # role name level-3 description Predefined level-3 role # role name level-4 description Predefined level-4 role # role name level-5 description Predefined level-5 role # role name level-6 description Predefined level-6 role # role name level-7 description Predefined level-7 role # role name level-8 description Predefined level-8 role # role name level-9 description Predefined level-9 role # role name level-10 description Predefined level-10 role # role name level-11 description Predefined level-11 role # role name level-12 description Predefined level-12 role # role name level-13 description Predefined level-13 role # role name level-14 description Predefined level-14 role # user-group system identity-member user accenture # local-user accenture class manage password hash $h$6$DkhDCTM3RYavMYHe$d+pz+Ex/uIINk7VKvUGpsWi4SH3bsGg3PAiY6JkrqqYirGLLaEefZ8085SBkRWqQx/YAFJNzmAM2hnUK3f2a+w== service-type ssh terminal http https authorization-attribute user-role level-3 authorization-attribute user-role network-admin authorization-attribute user-role network-operator # local-user admin class manage password hash $h$6$7IGhhyoWzvT0z4r5$tPhjs16TH+Eu8HhM3bmKKG1jzRUIo8lsGun2T/hLNOIhOabqG+GfPw8KJE0g0vLXa6G9NaerJ2h2fZOs0pP6qg== service-type ssh terminal https authorization-attribute user-role level-3 authorization-attribute user-role network-admin authorization-attribute user-role network-operator # ip https enable webui log enable # uapp-control # security-policy ip rule 0 name "Zone1 to Zone2" action pass counting enable source-zone Zone1 destination-zone Zone2 source-ip internet1 destination-ip internet2 service TCP_2404-2410 service AWS service BUFF service ssh service ping rule 1 name "Zone2 to Zone1" action pass counting enable source-zone Zone2 destination-zone Zone1 source-ip internet2 destination-ip internet1 service TCP_2404-2410 service ssh service ping rule 2 name "Zone2 to Zone1-1" action pass counting enable source-zone Zone2 destination-zone Zone1 source-ip internet2 destination-ip MON service ntp service ping rule 3 name "FEP to AGc" action pass counting enable source-zone Zone1 destination-zone AGC source-ip FEP1 source-ip FEP2 destination-ip AGC service TCP_2404 service ping rule 4 name "AGC to FEP" action pass counting enable source-zone AGC destination-zone Zone1 source-ip AGC destination-ip FEP1 destination-ip FEP2 service TCP_2404 service ping rule 5 name "FEP to YuanDong" action pass counting enable source-zone Zone1 destination-zone YuanDong source-ip FEP1 source-ip FEP2 destination-ip YuanDong1 destination-ip YuanDong2 service TCP_2404 service ping rule 6 name "YuanDong to FEP" action pass counting enable source-zone YuanDong destination-zone Zone1 source-ip YuanDong1 source-ip YuanDong2 destination-ip FEP1 destination-ip FEP2 service TCP_2404 service ping rule 7 name localout action pass counting enable source-zone Local destination-zone Zone1 destination-zone Zone2 destination-zone AGC destination-zone YuanDong rule 8 name localin action pass counting enable source-zone Zone1 source-zone Zone2 source-zone AGC source-zone YuanDong # return