ipsec野蛮模式第二阶段没起来
- 0关注
- 0收藏,1348浏览
问题描述:
两端接口都配置了 nat outbound , ipsec apply policy 1 , ipsec no-nat-process enable
《r3》 有出口IP的
ipsec transform-set 1
esp encryption-algorithm 3des-cbc
esp authentication-algorithm md5
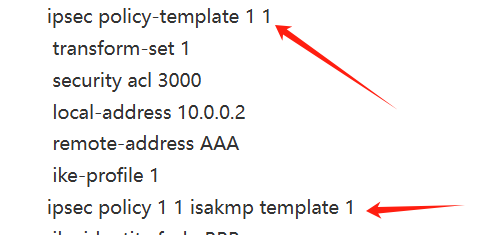
ipsec policy-template 1 1
transform-set 1
security acl 3000
local-address 10.0.0.2
remote-address AAA
ike-profile 1
ipsec policy 1 1 isakmp template 1
ike identity fqdn BBB
ike profile 1
keychain 1
exchange-mode aggressive
local-identity address 10.0.0.2
match remote identity fqdn AAA
proposal 1
ike proposal 1
encryption-algorithm 3des-cbc
authentication-algorithm md5
ike keychain 1
pre-shared-key hostname AAA key cipher $c$3$uP2+HZj7qf5MzppGxWg7QB0+tAshMzKPzQ==
<r1>接口IP自动获得的
ipsec transform-set 1
esp encryption-algorithm 3des-cbc
esp authentication-algorithm md5
ipsec policy 1 1 isakmp
transform-set 1
security acl 3000
remote-address 10.0.0.2
ike-profile 1
ike identity fqdn AAA
ike profile 1
keychain 1
exchange-mode aggressive
local-identity fqdn AAA
match remote identity address 10.0.0.2 255.255.255.255
proposal 1
ike proposal 1
encryption-algorithm 3des-cbc
authentication-algorithm md5
ike keychain 1
pre-shared-key address 10.0.0.2 255.255.255.255 key cipher $c$3$uY3epY6Z+3eHg2DyFoB4TKMWnoM0X4ZVjQ==
组网及组网描述:
麻烦大神帮忙看看什么问题
- 2025-04-01提问
- 举报
-
(0)
最佳答案

您好,第二阶段是ipsec 阶段
起不来看一下双方的加密算法协商是否一致
其次就是debugging IPSec
- 2025-04-01回答
- 评论(3)
- 举报
-
(0)
Can't find block-flow node.The reason of dropping packet is no available IPsec tunnel.
这是r3的 Received DNS analyse invalid result or have no address result.
提示找不到隧道

acl内容感兴趣流发一下
- 2025-04-01回答
- 评论(5)
- 举报
-
(0)
换了nat outbound 3100 拒绝流了,也不行
r1这侧是原192.168.1.0目的172.16.0.0 r3侧是原172.16.0.0 目的192.168.1.0
acl advanced 3000 rule 0 permit ip source 172.16.0.0 0.0.0.255 destination 192.168.1.0 0.0.0.255 acl advanced 3000 rule 0 permit ip source 192.168.1.0 0.0.0.255 destination 172.16.0.0 0.0.0.255 acl advanced 3000 rule 0 permit ip source 192.168.1.0 0.0.0.255 destination 172.16.0.0 0.0.0.255
换了nat outbound 3100 拒绝流了,也不行

策略需要在接口下应用,你配置了吗
这2个地方应该要一致,接口下应用的策略名和你配置都不一样
- 2025-04-01回答
- 评论(6)
- 举报
-
(0)
我调用的策略模版,野蛮模式就得这么配的
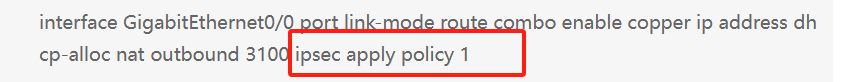
interface GigabitEthernet0/0 port link-mode route combo enable copper ip address dhcp-alloc nat outbound 3100 ipsec apply policy 1
肯定调用了啊
找到问题了,就是你这个截图里对端IP是没有的,我填的remote-address AAA,我把这个删了就通了
STRING<1-253> Host name of the remote peer 它这个提示对端主机名应该也是能填的,不清楚为啥删了就通了= =
我调用的策略模版,野蛮模式就得这么配的

用这种 中心节点---分支节点的方式试试吧 固定ip 当中心节点,自动获取充当分支
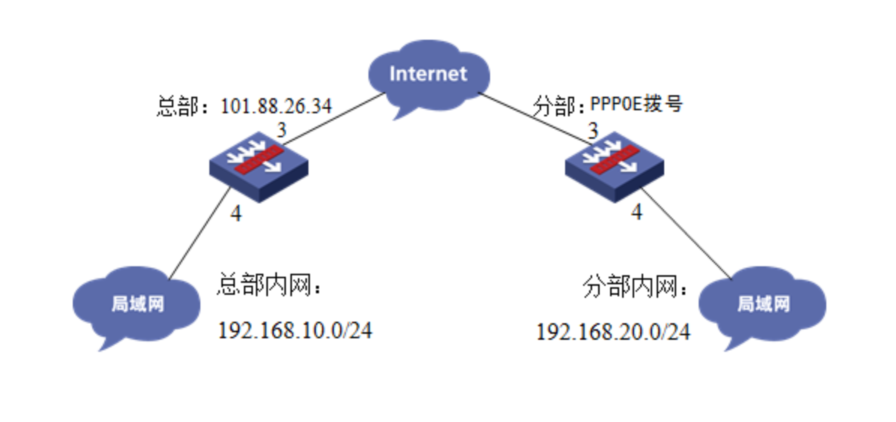
野蛮模式配置案例:
组网图
3 配置步骤
3.1 两端防火墙上网配置
防火墙上网配置请参考“2.3.2 防火墙外网使用固定IP地址上网配置方法”及“2.3.1 防火墙外网使用拨号上网配置方法”进行配置,本文只针对IPSEC VPN配置进行介绍。
3.2 总部侧排除IPSEC兴趣流不做NAT
#创建acl 3888调用在外网接口用于排除IPSEC兴趣流不做NAT。
[H3C]acl advanced 3888
[H3C-acl-ipv4-adv-3888]rule deny ip source 192.168.10.0 0.0.0.255 destination 192.168.20.0 0.0.0.255
[H3C-acl-ipv4-adv-3888]rule permit ip source any
[H3C-acl-ipv4-adv-3888]quit
3.3 总部侧创建IPSEC安全提议
#加密类型设置为aes-cbc-128,认证类型设置为sha1。
[H3C]ipsec transform-set GE1/0/3_IPv4_1
[H3C-ipsec-transform-set-1] esp encryption-algorithm aes-cbc-128
[H3C-ipsec-transform-set-1] esp authentication-algorithm sha1
[H3C-ipsec-transform-set-1]quit
3.4 总部侧创建IKE安全提议
#IKE安全提议默认的认证类型为sha1,加密类型为DES-CBC,DH组为DH1,所以不需要配置也存在这些参数。
[H3C]ike proposal 1
[H3C-ike-proposal-1]quit
3.5 总部侧创建IKE安全密钥
#创建IKE密钥,地址填写0.0.0.0/0,密码设置为123456。
[H3C]ike keychain 1
[H3C-ike-keychain-1]pre-shared-key address 0.0.0.0 0.0.0.0 key simple 123456
[H3C-ike-keychain-1]quit
3.6 总部侧创建IKE安全框架
#创建IKE安全框架,协商模式调整为野蛮模式。本端身份识别为center,分部身份识别为branch。
[H3C]ike profile 1
[H3C-ike-profile-1]keychain 1
[H3C-ike-profile-1] exchange-mode aggressive
[H3C-ike-profile-1] local-identity fqdn center
[H3C-ike-profile-1]match remote identity address 0.0.0.0 0.0.0.0
[H3C-ike-profile-1]match remote identity fqdn branch
[H3C-ike-profile-1]proposal 1
[H3C-ike-profile-1]quit
3.7 总部侧创建IPSEC安全策略模板
[H3C]ipsec policy-template GE1/0/3 1
[H3C-ipsec-policy- template-GE1/0/3-1]transform-set GE1/0/3_IPv4_1
[H3C-ipsec-policy- template-GE1/0/3-1]local-address 101.88.26.34
[H3C-ipsec-policy- template-GE1/0/3-1]ike-profile 1
[H3C-ipsec-policy- template-GE1/0/3-1]quit
3.8 总部侧创建IPSEC安全策略
#创建IKE安全策略GE1/0/3将安全策略模板和安全策略绑定。
[H3C]ipsec policy GE1/0/3 1 isakmp template GE1/0/3
3.9 总部侧外网接口调用IPSEC策略和NAT动态转换策略
[H3C]interface GigabitEthernet 1/0/3
[H3C-GigabitEthernet1/0/3]ipsec apply policy GE1/0/3
[H3C-GigabitEthernet1/0/3]nat outbound 3888
[H3C-GigabitEthernet1/0/3]quit
3.10 保存配置
[H3C]save force
3.11 分部侧创建IPSEC兴趣流匹配到总部的数据
#创建IPSEC的感兴趣流,用于匹配IPSEC数据。
<H3C>system
[H3C]acl advanced 3999
[H3C-acl-ipv4-adv-3999]rule permit ip source 192.168.20.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
[H3C-acl-ipv4-adv-3999]quit
#创建acl 3888调用在外网接口用于排除IPSEC兴趣流不做NAT。
[H3C]acl advanced 3888
[H3C-acl-ipv4-adv-3888]rule deny ip source 192.168.20.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
[H3C-acl-ipv4-adv-3888]rule permit ip source any
[H3C-acl-ipv4-adv-3888]quit
3.12 分部侧创建IPSEC安全提议
#加密类型设置为aes-cbc-128,认证类型设置为sha1。
[H3C]ipsec transform-set GE1/0/3_IPv4_1
[H3C-ipsec-transform-set-1] esp encryption-algorithm aes-cbc-128
[H3C-ipsec-transform-set-1] esp authentication-algorithm sha1
[H3C-ipsec-transform-set-1]quit
3.13 分部侧创建IKE安全提议
#IKE安全提议默认的认证类型为sha1,加密类型为DES-CBC,DH组为DH1,所以不需要配置也存在这些参数。
[H3C]ike proposal 1
[H3C-ike-proposal-1]quit
3.14 分部侧创建IKE安全密钥
#创建IKE密钥,地址填写总部侧设备的公网IP,密码设置为123456。
[H3C]ike keychain 1
[H3C-ike-keychain-1] pre-shared-key address 101.88.26.34 255.255.255.255 key simple 123456
[H3C-ike-keychain-1]quit
3.15 分部侧创建IKE安全框架
#创建IKE安全框架,匹配keychain 1安全密匙,协商模式调整为野蛮模式。本端身份识别为branch,分部身份识别为center,并制定对端地址为总部侧公网地址。
[H3C]ike profile 1
[H3C-ike-profile-1]keychain 1
[H3C-ike-profile-1]exchange-mode aggressive
[H3C-ike-profile-1] local-identity fqdn branch
[H3C-ike-profile-1] match remote identity fqdn center
[H3C-ike-profile-1] match remote identity address 101.88.26.34 255.255.255.255
[H3C-ike-profile-1]proposal 1
[H3C-ike-profile-1]quit
3.16 分部侧创建IPSEC安全策略
#创建IKE安全策略GE1/0/3将transform-set、acl、ike-profile、本端地址、对端地址关联起来。
[H3C]ipsec policy GE1/0/3 1 isakmp
[H3C-ipsec-policy-isakmp-GE1/0/3-1] transform-set GE1/0/3_IPv4_1
[H3C-ipsec-policy-isakmp-GE1/0/3-1]security acl 3999
[H3C-ipsec-policy-isakmp-GE1/0/3-1] remote-address 101.88.26.34
[H3C-ipsec-policy-isakmp-GE1/0/3-1]ike-profile 1
[H3C-ipsec-policy-isakmp-GE1/0/3-1]quit
3.17 分部侧外网接口调用IPSEC策略和NAT动态转换策略
[H3C]interface dialer 1
[H3C-Dialer1]ipsec apply policy GE1/0/3
[H3C-Dialer1]nat outbound 3888
[H3C-Dialer1]quit
3.18 保存配置
[H3C]save force
3.19 隧道验证
#分部通过命令行查看display ike sa可以看到隧道状态为RD状态表示ike建立完成。
分支通过display ipsec sa可以看到IPSEC SA基本状态。
#总部通过命令行查看display ike sa可以看到隧道状态为RD状态表示ike建立完成。
#分支通过display ipsec sa可以看到IPSEC SA基本状态。
- 2025-04-01回答
- 评论(1)
- 举报
-
(0)
我就是这么配的,只是总部侧虚模版里多打了个对端主机名,就没起来
我就是这么配的,只是总部侧虚模版里多打了个对端主机名,就没起来
编辑答案


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明




提示找不到隧道