两台H3C路由器互联配置后,网关互ping不通
- 0关注
- 1收藏,3353浏览
问题描述:
这是两台路由器的配置,各位大神能给指导指导吗?
站端
<zhanduan1>dis cu
#
version 5.20, Release 1508P02, Standard
#
sysname zhanduan1
#
clock timezone Beijing add 08:00:00
#
domain default enable system
#
router id 37.2.92.160
#
ip vpn-instance vpn-rt
route-distinguisher 23726:1
vpn-target 23726:101 export-extcommunity
vpn-target 23726:100 20000:100 30000:100 import-extcommunity
#
ip vpn-instance vpn-nrt
route-distinguisher 23726:2
vpn-target 23726:201 export-extcommunity
vpn-target 23726:200 20000:200 30000:200 import-extcommunity
#
ip vpn-instance vpn-pw
route-distinguisher 23726:4
vpn-target 23726:401 export-extcommunity
vpn-target 23726:400 import-extcommunity
#
vlan 1
#
vlan 10
description NMS
#
vlan 199
description To_vpn-rt
#
vlan 299
description To_vpn-nrt
#
vlan 499
description To_vpn-pw
#
mpls lsr-id 37.2.92.160
#
mpls
#
mpls ldp
#
domain system
access-limit disable
state active
idle-cut disable
self-service-url disable
#
local-user bzzdh
password cipher IV/L%>K11XF,YWX*NZ55OA!!
service-type ssh terminal
#
acl number 2000
rule 1 permit source 37.172.0.250 0
rule 2 permit source 37.172.0.200 0
rule 3 permit source 37.172.160.1 0
rule 5 deny
acl number 2001
rule 1 permit source 37.172.0.250 0
#
acl number 3001
rule 0 deny tcp destination-port eq 135
rule 5 deny tcp destination-port eq 137
rule 10 deny tcp destination-port eq 138
rule 15 deny tcp destination-port eq 139
rule 20 deny tcp destination-port eq 445
rule 25 deny udp destination-port eq 135
rule 30 deny udp destination-port eq netbios-ns
rule 35 deny udp destination-port eq netbios-dgm
rule 40 deny udp destination-port eq netbios-ssn
rule 45 deny udp destination-port eq 445
#
interface Aux0
async mode flow
link-protocol ppp
#
interface Serial6/0
link-protocol ppp
#
interface Serial6/1
link-protocol ppp
#
interface Serial6/2
link-protocol ppp
#
interface Serial6/3
link-protocol ppp
#
interface NULL0
#
interface LoopBack0
ip address 37.2.92.160 255.255.255.255
#
interface GigabitEthernet0/0
port link-mode route
ip address 192.168.1.1 255.255.255.0
#
interface GigabitEthernet0/0.10
vlan-type dot1q vid 10
description To_NMS
ip address 37.172.160.30 255.255.255.240
#
interface GigabitEthernet0/0.199
vlan-type dot1q vid 199
description to vpn-rt
ip binding vpn-instance vpn-rt
ip address 37.173.160.126 255.255.255.128
#
interface GigabitEthernet0/0.299
vlan-type dot1q vid 299
description to vpn-nrt
ip binding vpn-instance vpn-nrt
ip address 37.174.160.126 255.255.255.128
#
interface GigabitEthernet0/1
port link-mode route
ip address 37.172.160.2 255.255.255.252
ospf cost 10
mpls
mpls ldp
#
bgp 23726
undo synchronization
timer keepalive 5 hold 15
group hexin internal
peer hexin connect-interface LoopBack0
peer 37.2.92.170 group hexin
#
ipv4-family vpnv4
peer hexin enable
peer 37.2.92.170 enable
peer 37.2.92.170 group hexin
#
ipv4-family vpn-instance vpn-rt
import-route direct
#
ipv4-family vpn-instance vpn-nrt
import-route direct
#
ipv4-family vpn-instance vpn-pw
import-route direct
#
ospf 1
import-route direct
area 0.0.0.1
network 37.172.160.0 0.0.0.3
#
ip route-static 37.172.160.0 255.255.255.252 37.172.160.1
ip route-static 37.173.0.0 255.255.0.0 37.172.160.1
ip route-static 37.174.0.0 255.255.0.0 37.172.160.1
#
ssh server enable
#
user-interface con 0
user-interface aux 0
user-interface vty 0 4
acl 2000 inbound
authentication-mode scheme
idle-timeout 5 0
protocol inbound ssh
#
return
核心
<hexin>dis cu
#
version 5.20, Release 1508P02, Standard
#
sysname hexin
#
clock timezone Beijing add 08:00:00
#
domain default enable system
#
router id 37.2.92.170
#
ip vpn-instance vpn-rt
route-distinguisher 23726:1
vpn-target 23726:100 20000:100 30000:100 export-extcommunity
vpn-target 23726:101 23726:100 30000:100 20000:100 import-extcommunity
#
ip vpn-instance vpn-nrt
route-distinguisher 23726:2
vpn-target 23726:201 export-extcommunity
vpn-target 23726:200 20000:200 30000:200 import-extcommunity
#
ip vpn-instance vpn-pw
route-distinguisher 23726:4
vpn-target 23726:401 export-extcommunity
vpn-target 23726:400 import-extcommunity
#
vlan 1
#
vlan 10
description NMS
#
vlan 199
description To_vpn-rt
#
vlan 299
description To_vpn-nrt
#
vlan 499
description To_vpn-pw
#
mpls lsr-id 37.2.92.170
#
mpls
#
mpls ldp
#
domain system
access-limit disable
state active
idle-cut disable
self-service-url disable
#
local-user admin
password cipher H;-]Ma5VSZD=`&4T-(O7UH*2_*aAEH84Z7W/O2`\89H>(,<4Z,BO&L"TX$_S#6.NM(0=0\)*5WWQ=^Q`MAF4<1!!
service-type telnet
local-user bzzdh
password cipher IV/L%>K11XF,YWX*NZ55OA!!
service-type ssh terminal
#
acl number 2000
rule 1 permit source 37.172.0.250 0
rule 2 permit source 37.172.0.200 0
rule 3 permit source 37.172.160.1 0
rule 5 deny
acl number 2001
rule 1 permit source 37.172.0.250 0
#
acl number 3001
rule 0 deny tcp destination-port eq 135
rule 5 deny tcp destination-port eq 137
rule 10 deny tcp destination-port eq 138
rule 15 deny tcp destination-port eq 139
rule 20 deny tcp destination-port eq 445
rule 25 deny udp destination-port eq 135
rule 30 deny udp destination-port eq netbios-ns
rule 35 deny udp destination-port eq netbios-dgm
rule 40 deny udp destination-port eq netbios-ssn
rule 45 deny udp destination-port eq 445
#
interface Aux0
async mode flow
link-protocol ppp
#
interface Serial6/0
link-protocol ppp
#
interface Serial6/1
link-protocol ppp
#
interface Serial6/2
link-protocol ppp
#
interface Serial6/3
link-protocol ppp
#
interface NULL0
#
interface LoopBack0
ip address 37.2.92.170 255.255.255.255
#
interface GigabitEthernet0/0
port link-mode route
ip address 192.168.1.1 255.255.255.0
#
interface GigabitEthernet0/0.10
vlan-type dot1q vid 10
description To_NMS
ip address 37.172.170.30 255.255.255.240
#
interface GigabitEthernet0/0.199
vlan-type dot1q vid 199
description vpn-rt
ip binding vpn-instance vpn-rt
ip address 37.173.170.126 255.255.255.128
#
interface GigabitEthernet0/0.299
vlan-type dot1q vid 299
description vpn-nrt
ip binding vpn-instance vpn-nrt
ip address 37.174.92.126 255.255.255.128
#
interface GigabitEthernet0/1
port link-mode route
description to zhuanduan1
ip address 37.172.160.1 255.255.255.252
ospf cost 10
#
bgp 23726
undo synchronization
timer keepalive 5 hold 15
group zhanduan1 internal
peer zhanduan1 connect-interface LoopBack0
peer 37.2.92.160 group zhanduan1
#
ipv4-family vpnv4
peer zhanduan1 enable
peer zhanduan1 route-policy Deny-DD-Sum-Pri export
peer 37.2.92.160 enable
peer 37.2.92.160 group zhanduan1
#
ipv4-family vpn-instance vpn-rt
import-route direct
#
ipv4-family vpn-instance vpn-nrt
import-route direct
#
ospf 1
import-route direct
area 0.0.0.1
description to zhanduan
network 37.172.160.0 0.0.0.3
#
ip route-static 37.173.0.0 255.255.0.0 37.172.160.2
ip route-static 37.173.160.0 255.255.255.0 37.172.160.2
ip route-static 37.174.0.0 255.255.0.0 37.172.160.2
#
user-interface con 0
authentication-mode scheme
idle-timeout 5 0
user-interface aux 0
user-interface vty 0 4
acl 2000 inbound
authentication-mode scheme
idle-timeout 5 0
protocol inbound ssh
#
return
<hexin>ping -vpn-instance vpn-rt 37.173.170.2
PING 37.173.170.2: 56 data bytes, press CTRL_C to break
Reply from 37.173.170.2: bytes=56 Sequence=1 ttl=128 time=1 ms
Reply from 37.173.170.2: bytes=56 Sequence=2 ttl=128 time=1 ms
Reply from 37.173.170.2: bytes=56 Sequence=3 ttl=128 time=1 ms
Reply from 37.173.170.2: bytes=56 Sequence=4 ttl=128 time=1 ms
Reply from 37.173.170.2: bytes=56 Sequence=5 ttl=128 time=1 ms
--- 37.173.170.2 ping statistics ---
5 packet(s) transmitted
5 packet(s) received
0.00% packet loss
round-trip min/avg/max = 1/1/1 ms
<hexin>ping -vpn-instance vpn-rt 37.173.160.126
PING 37.173.160.126: 56 data bytes, press CTRL_C to break
Request time out
Request time out
Request time out
Request time out
Request time out
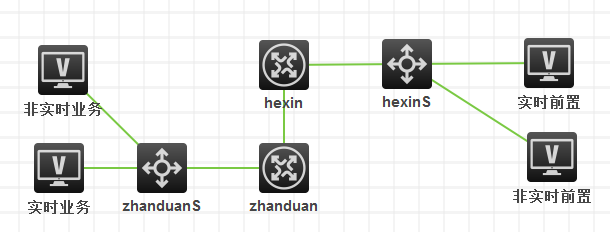
组网及组网描述:
- 2019-09-11提问
- 举报
-
(0)
最佳答案

问题
- 2019-09-11回答
- 评论(2)
- 举报
-
(0)


先看看路由学到没
- 2019-09-11回答
- 评论(1)
- 举报
-
(0)
有到loopback地址的路由,业务的加的静态路由
有到loopback地址的路由,业务的加的静态路由
编辑答案


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明


没注意到你把直连宣告到OSPF,BGP确实能起来.但是你的MPLS,起不来,你上面的配置就没使能