问
F100-A-G2防火墙如何配置ipsec?
2019-10-31提问
- 0关注
- 1收藏,2461浏览
问题描述:
对端是Er3200G2路由器,且已参考官方文档配好ipsec。本端是F100-A-G2防火墙,配好了ipsec,但是无法连通对端。
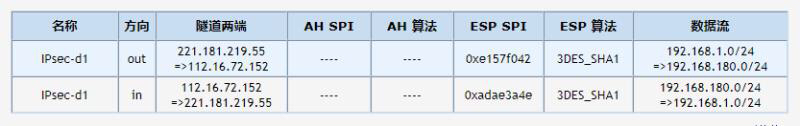
对端ER3200G2上查看隧道,如下图:
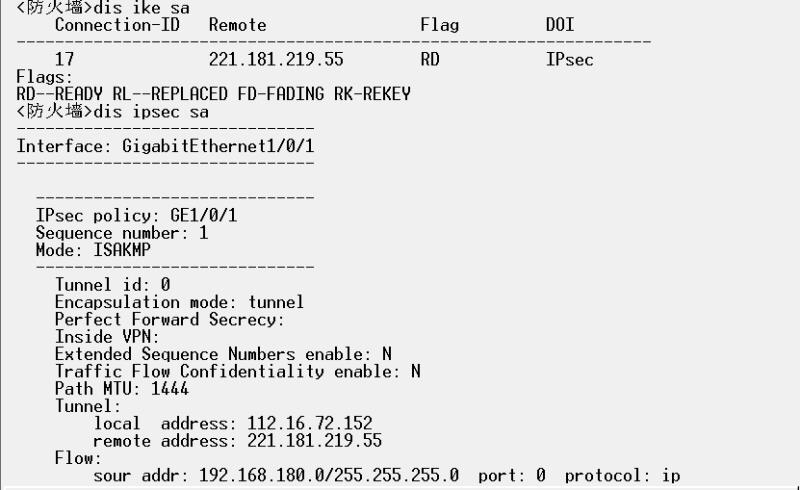
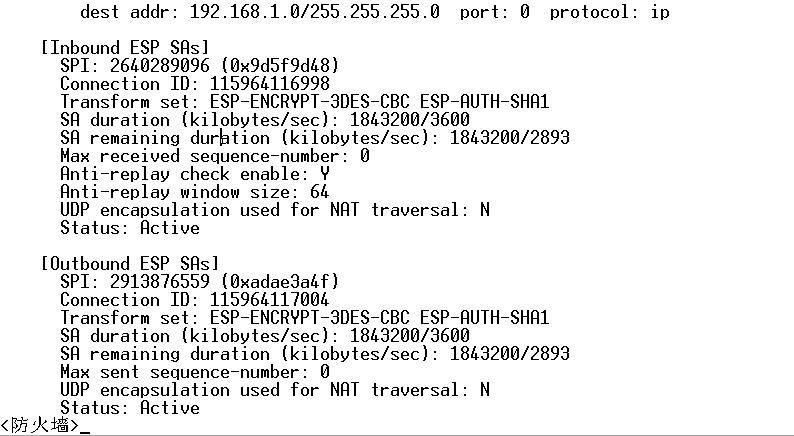
本端防火墙上查看隧道,如下图:
求大神帮忙看下配置和路由哪里有问题,感激不尽。
组网及组网描述:
组网:F100-A-G2--s5500三层--s3100--PC
网关在三层的5500上,防火墙Nat出口。
防火墙配置如下: (底下还有5500的配置)
#
version 7.1.064, Ess 9310P12
#
sysname 防火墙
#
clock timezone Beijing add 08:00:00
clock protocol none
#
context Admin id 1
#
ip vpn-instance management
route-distinguisher 1000000000:1
vpn-target 1000000000:1 import-extcommunity
vpn-target 1000000000:1 export-extcommunity
#
irf mac-address persistent timer
irf auto-update enable
undo irf link-delay
irf member 1 priority 1
#
password-recovery enable
#
vlan 1
#
object-group ip address 192.168.1.0
0 network subnet 192.168.1.0 255.255.255.0
#
object-group ip address 192.168.180.0
description Internet-lab
0 network subnet 192.168.180.0 255.255.255.0
#
object-group ip address 192.168.200.0
description 709 Internet-Zone
0 network subnet 192.168.200.0 255.255.255.0
#
object-group ip address 192.168.208.0
description 708-PC
0 network subnet 192.168.208.0 255.255.255.0
#
object-group ip address 192.168.209.0
description 709-PC
0 network subnet 192.168.209.0 255.255.255.0
#
object-group ip address 192.168.210.0
description 710-PC
0 network subnet 192.168.210.0 255.255.255.0
#
object-group ip address 192.168.212.0
description 712-PC
0 network subnet 192.168.212.0 255.255.255.0
#
object-group ip address 192.168.255.240
description Switch manager
0 network subnet 192.168.255.240 255.255.255.240
#
object-group ip address 192.168.36.0
description Intranet-Server-No Isolation
0 network subnet 192.168.36.0 255.255.255.0
#
object-group ip address 192.168.36.6
description 内部主DNS
0 network host address 192.168.36.6
#
object-group ip address 192.168.36.66
description 辅DNS
0 network host address 192.168.36.66
#
object-group ip address 192.168.60.0
description Intranet-Server-Isolation
0 network subnet 192.168.60.0 255.255.255.0
#
object-group ip address 192.168.66.0
description Internet-Server-No Isolation
0 network subnet 192.168.66.0 255.255.255.0
#
object-group ip address 192.168.88.0
description Internet-PC
0 network subnet 192.168.88.0 255.255.255.0
#
object-group ip address 211.140.13.188
description 外部DNS
0 network host address 211.140.13.188
#
interface NULL0
#
interface GigabitEthernet1/0/0
port link-mode route
ip binding vpn-instance management
#
interface GigabitEthernet1/0/1
port link-mode route
description To移动(WAN)
duplex full
ip address 112.16.72.152 255.255.255.128
nat outbound 3000
nat server protocol udp global current-interface 5060 inside 192.168.180.33 5060 disable
ipsec apply policy GE1/0/1
#
interface GigabitEthernet1/0/2
port link-mode route
#
interface GigabitEthernet1/0/3
port link-mode route
description Management
ip address 10.80.0.1 255.255.255.252
#
interface GigabitEthernet1/0/4
port link-mode route
#
interface GigabitEthernet1/0/5
port link-mode route
#
interface GigabitEthernet1/0/6
port link-mode route
#
interface GigabitEthernet1/0/7
port link-mode route
#
interface GigabitEthernet1/0/8
port link-mode route
#
interface GigabitEthernet1/0/9
port link-mode route
#
interface GigabitEthernet1/0/10
port link-mode route
#
interface GigabitEthernet1/0/11
port link-mode route
#
interface GigabitEthernet1/0/12
port link-mode route
#
interface GigabitEthernet1/0/13
port link-mode route
#
interface GigabitEthernet1/0/14
port link-mode route
#
interface GigabitEthernet1/0/15
port link-mode route
description LAN
duplex full
speed 1000
ip address 192.168.255.242 255.255.255.240
nat hairpin enable
#
interface GigabitEthernet1/0/16
port link-mode route
#
interface GigabitEthernet1/0/17
port link-mode route
#
interface GigabitEthernet1/0/18
port link-mode route
#
interface GigabitEthernet1/0/19
port link-mode route
#
interface GigabitEthernet1/0/20
port link-mode route
#
interface GigabitEthernet1/0/21
port link-mode route
#
interface GigabitEthernet1/0/22
port link-mode route
#
interface GigabitEthernet1/0/23
port link-mode route
#
object-policy ip Local-Untrust
rule 0 pass
#
object-policy ip Trust-Untrust
rule 0 pass source-ip 192.168.66.0
rule 0 comment Internet-Server-No Isolation
rule 1 pass source-ip 192.168.88.0
rule 1 comment Internet-PC
rule 2 pass source-ip 192.168.180.0
rule 2 comment Internet-lab
rule 3 pass source-ip 192.168.36.6 destination-ip 211.140.13.188
rule 3 comment 主DNS转发
rule 4 pass source-ip 192.168.36.66 destination-ip 211.140.13.188
rule 4 comment 辅DNS
#
object-policy ip Untrust-Local
rule 0 pass
#
object-policy ip Untrust-Trust
rule 0 pass source-ip 192.168.1.0 destination-ip 192.168.180.0
#
security-zone name Local
#
security-zone name Trust
import interface GigabitEthernet1/0/15
#
security-zone name DMZ
#
security-zone name Untrust
import interface GigabitEthernet1/0/1
#
security-zone name Management
import interface GigabitEthernet1/0/3
#
zone-pair security source Local destination Untrust
object-policy apply ip Local-Untrust
#
zone-pair security source Trust destination Untrust
object-policy apply ip Trust-Untrust
#
zone-pair security source Untrust destination Local
object-policy apply ip Untrust-Local
#
zone-pair security source Untrust destination Trust
object-policy apply ip Untrust-Trust
#
scheduler logfile size 16
#
line class aux
user-role network-operator
#
line class console
user-role network-admin
#
line class vty
user-role network-operator
#
line aux 0
user-role network-admin
#
line con 0
authentication-mode scheme
user-role network-admin
#
line vty 0 63
authentication-mode scheme
user-role network-admin
#
ip route-static 0.0.0.0 0 112.16.72.254
ip route-static 192.168.1.0 24 192.168.255.241
ip route-static 192.168.36.0 24 192.168.255.241
ip route-static 192.168.66.0 24 192.168.255.241 description Internet-Server-No Isolation
ip route-static 192.168.88.0 24 192.168.255.241 description Internet-PC
ip route-static 192.168.180.0 24 192.168.255.241 description Internet-lab
#
snmp-agent
snmp-agent local-engineid 800063A28084D9318BEA1700000001
snmp-agent sys-info contact 15021202522
snmp-agent sys-info location 711
snmp-agent sys-info version v3
#
ntp-service source GigabitEthernet1/0/1
#
acl advanced 3000
rule 0 permit ip source 192.168.66.0 0.0.0.255
rule 0 comment Internet-Server-No Isolation
rule 5 permit ip source 192.168.88.0 0.0.0.255
rule 5 comment Internet-PC
rule 10 permit ip source 192.168.180.0 0.0.0.255
rule 10 comment Internet-lab
rule 15 permit ip source 192.168.36.6 0 destination 211.140.13.188 0
rule 15 comment 主DNS
rule 20 permit ip source 192.168.36.66 0 destination 211.140.13.188 0
rule 20 comment 辅DNS
#
domain system
#
aaa session-limit ftp 16
aaa session-limit telnet 16
aaa session-limit ssh 16
domain default enable system
#
role name level-0
description Predefined level-0 role
#
role name level-1
description Predefined level-1 role
#
role name level-2
description Predefined level-2 role
#
role name level-3
description Predefined level-3 role
#
role name level-4
description Predefined level-4 role
#
role name level-5
description Predefined level-5 role
#
role name level-6
description Predefined level-6 role
#
role name level-7
description Predefined level-7 role
#
role name level-8
description Predefined level-8 role
#
role name level-9
description Predefined level-9 role
#
role name level-10
description Predefined level-10 role
#
role name level-11
description Predefined level-11 role
#
role name level-12
description Predefined level-12 role
#
role name level-13
description Predefined level-13 role
#
role name level-14
description Predefined level-14 role
#
user-group system
#
local-user admin class manage
password hash $h$6$jXnlWbUZ8j8e02ID$9KvJSKTVq+TapX57Cyk7qOn0PkBd8YAygQmxnTmh3CGBavNuEPArDwQAgVw37HIEC8rIiiauJClaCRmRANlQzA==
service-type ssh terminal https
authorization-attribute user-role level-3
authorization-attribute user-role network-admin
authorization-attribute user-role network-operator
#
local-user quadmin class manage
password hash $h$6$AArDSL9yvOm7/wr8$Aj/X2aLFCbww2PpFl3eHoRjnh3ULytu3BiCJCDBubiHmae6b3quXUzhq6gFBibT4p9abptgYw7ihrijopjBbUQ==
service-type ssh terminal http https
authorization-attribute work-directory slot1#flash:
authorization-attribute user-role level-3
authorization-attribute user-role network-admin
authorization-attribute user-role network-operator
#
ipsec transform-set GE1/0/1_IPv4_1
esp encryption-algorithm 3des-cbc
esp authentication-algorithm sha1
#
ipsec policy GE1/0/1 1 isakmp
transform-set GE1/0/1_IPv4_1
security acl 3000
remote-address 221.181.219.55
description vpn
ike-profile GE1/0/1_IPv4_1
#
nat alg h323
nat alg ils
nat alg mgcp
nat alg nbt
nat alg rsh
nat alg sccp
nat alg sip
nat alg sqlnet
nat alg tftp
nat alg xdmcp
#
ike profile GE1/0/1_IPv4_1
keychain GE1/0/1_IPv4_1
local-identity address 112.16.72.152
match remote identity address 221.181.219.55 255.255.255.240
match local address GigabitEthernet1/0/1
proposal 65535
#
ike proposal 65535
encryption-algorithm 3des-cbc
dh group2
description GE1/0/1_IPv4_1
#
ike keychain GE1/0/1_IPv4_1
match local address GigabitEthernet1/0/1
pre-shared-key address 221.181.219.55 255.255.255.240 key cipher $c$3$/bFpoItYRgE9fGXqtAQb/57nUi6cK/WfSw==
#
ip https enable
#
inspect block-source parameter-profile ips_block_default_parameter
#
inspect capture parameter-profile ips_capture_default_parameter
#
inspect logging parameter-profile ips_logging_default_parameter
#
inspect redirect parameter-profile av_redirect_default_parameter
#
inspect redirect parameter-profile ips_redirect_default_parameter
#
inspect redirect parameter-profile url_redirect_default_parameter
#
loadbalance action ##defaultactionforllbipv4##%%autocreatedbyweb%% type link-generic
forward all
#
loadbalance policy ##defaultpolicyforllbipv4##%%autocreatedbyweb%% type link-generic
default-class action ##defaultactionforllbipv4##%%autocreatedbyweb%%
#
virtual-server ##defaultvsforllbipv4##%%autocreatedbyweb%% type link-ip
virtual ip address 0.0.0.0 0
lb-policy ##defaultpolicyforllbipv4##%%autocreatedbyweb%%
bandwidth interface statistics enable
#
traffic-policy
#
ips policy default
#
anti-virus policy default
#
return
以下为5500配置
#
version 5.20, Release 2220P02
#
sysname S5500-709
#
clock timezone Beijing add 08:00:00
#
dhcp relay server-group 1 ip 192.168.36.6
#
irf mac-address persistent timer
irf auto-update enable
undo irf link-delay
#
domain default enable system
#
password-recovery enable
#
acl number 3100
rule 0 permit ip source 192.168.180.0 0.0.0.255 destination 192.168.36.0 0.0.0.255
rule 5 permit ip source 192.168.180.0 0.0.0.255 destination 192.168.66.0 0.0.0.255
rule 10 permit ip source 192.168.180.0 0.0.0.255 destination 192.168.111.0 0.0.0.255
rule 15 permit ip source 192.168.180.0 0.0.0.255 destination 192.168.1.0 0.0.0.255
rule 50 deny ip source 192.168.180.0 0.0.0.255 destination 192.168.0.0 0.0.255.255
acl number 3101
rule 0 permit ip source 192.168.200.0 0.0.0.255 destination 192.168.36.0 0.0.0.255
rule 5 permit ip source 192.168.200.0 0.0.0.255 destination 192.168.66.0 0.0.0.255
rule 10 permit ip source 192.168.200.0 0.0.0.255 destination 192.168.88.0 0.0.0.255
rule 50 deny ip source 192.168.200.0 0.0.0.255 destination 192.168.0.0 0.0.255.255
acl number 3102
rule 0 permit ip source 192.168.208.0 0.0.0.255 destination 192.168.36.0 0.0.0.255
rule 5 permit ip source 192.168.208.0 0.0.0.255 destination 192.168.66.0 0.0.0.255
rule 50 deny ip source 192.168.208.0 0.0.0.255 destination 192.168.0.0 0.0.255.255
acl number 3103
rule 0 permit ip source 192.168.209.0 0.0.0.255 destination 192.168.36.0 0.0.0.255
rule 5 permit ip source 192.168.209.0 0.0.0.255 destination 192.168.66.0 0.0.0.255
rule 50 deny ip source 192.168.209.0 0.0.0.255 destination 192.168.0.0 0.0.255.255
acl number 3104
rule 0 permit ip source 192.168.210.0 0.0.0.255 destination 192.168.36.0 0.0.0.255
rule 5 permit ip source 192.168.210.0 0.0.0.255 destination 192.168.66.0 0.0.0.255
rule 10 permit ip source 192.168.210.0 0.0.0.255 destination 192.168.255.240 0.0.0.15
rule 15 permit ip source 192.168.210.0 0.0.0.255 destination 192.168.111.0 0.0.0.255
rule 50 deny ip source 192.168.210.0 0.0.0.255 destination 192.168.0.0 0.0.255.255
acl number 3105
rule 0 permit ip source 192.168.212.0 0.0.0.255 destination 192.168.36.0 0.0.0.255
rule 5 permit ip source 192.168.212.0 0.0.0.255 destination 192.168.66.0 0.0.0.255
rule 10 permit ip source 192.168.212.0 0.0.0.255 destination 192.168.88.199 0
rule 50 deny ip source 192.168.212.0 0.0.0.255 destination 192.168.0.0 0.0.255.255
#
vlan 1
#
vlan 100
description 36 Intranet-Server-No isolation
#
vlan 101
description 60 Intranet-Server-Isolation
#
vlan 102
description 66 Internet-Server-No isolation
#
vlan 103
description 88 Internet-PC
#
vlan 104
description 180 711-Internet-lab
#
vlan 106
description 200 709-Internet Zone
#
vlan 107
description 208 708-PC
#
vlan 108
description 209 709-PC
#
vlan 109
description 210 710-PC
#
vlan 110
description 212 712-PC
#
vlan 111
description printf
#
vlan 900
description 225.240 Switch
#
domain system
access-limit disable
state active
idle-cut disable
self-service-url disable
#
user-group system
group-attribute allow-guest
#
local-user quadmin
password cipher $c$3$tzs5O4zlXaYRD+4a2VEcg4wJPTDlGB1rphgl5WSqOKc=
authorization-attribute level 3
service-type telnet
service-type ftp
service-type web
#
interface NULL0
#
interface Vlan-interface100
ip address 192.168.36.1 255.255.255.0
dhcp select relay
dhcp relay server-select 1
#
interface Vlan-interface101
ip address 192.168.60.1 255.255.255.0
dhcp select relay
dhcp relay server-select 1
#
interface Vlan-interface102
ip address 192.168.66.1 255.255.255.0
dhcp select relay
dhcp relay server-select 1
#
interface Vlan-interface103
ip address 192.168.88.1 255.255.255.0
dhcp select relay
dhcp relay server-select 1
#
interface Vlan-interface104
ip address 192.168.180.1 255.255.255.0
dhcp select relay
dhcp relay server-select 1
packet-filter 3100 inbound
#
interface Vlan-interface106
ip address 192.168.200.1 255.255.255.0
dhcp select relay
dhcp relay server-select 1
packet-filter 3101 inbound
#
interface Vlan-interface107
ip address 192.168.208.1 255.255.255.0
dhcp select relay
dhcp relay server-select 1
packet-filter 3102 inbound
#
interface Vlan-interface108
ip address 192.168.209.1 255.255.255.0
dhcp select relay
dhcp relay server-select 1
#
interface Vlan-interface109
ip address 192.168.210.1 255.255.255.0
dhcp select relay
dhcp relay server-select 1
packet-filter 3104 inbound
#
interface Vlan-interface110
ip address 192.168.212.1 255.255.255.0
dhcp select relay
dhcp relay server-select 1
packet-filter 3105 inbound
#
interface Vlan-interface111
ip address 192.168.111.1 255.255.255.0
#
interface Vlan-interface900
ip address 192.168.255.241 255.255.255.240
undo dhcp select server global-pool
#
interface GigabitEthernet1/0/1
port link-type trunk
port trunk permit vlan 1 900
port trunk pvid vlan 900
#
interface GigabitEthernet1/0/2
#
interface GigabitEthernet1/0/3
#
interface GigabitEthernet1/0/4
#
interface GigabitEthernet1/0/5
#
interface GigabitEthernet1/0/6
#
interface GigabitEthernet1/0/7
#
interface GigabitEthernet1/0/8
#
interface GigabitEthernet1/0/9
#
interface GigabitEthernet1/0/10
#
interface GigabitEthernet1/0/11
#
interface GigabitEthernet1/0/12
#
interface GigabitEthernet1/0/13
port access vlan 102
#
interface GigabitEthernet1/0/14
port access vlan 101
#
interface GigabitEthernet1/0/15
port link-type trunk
port trunk permit vlan all
#
interface GigabitEthernet1/0/16
#
interface GigabitEthernet1/0/17
port link-type trunk
port trunk permit vlan all
#
interface GigabitEthernet1/0/18
#
interface GigabitEthernet1/0/19
port link-type trunk
port trunk permit vlan all
#
interface GigabitEthernet1/0/20
#
interface GigabitEthernet1/0/21
port link-type trunk
port trunk permit vlan all
#
interface GigabitEthernet1/0/22
port access vlan 100
#
interface GigabitEthernet1/0/23
port link-type trunk
port trunk permit vlan all
#
interface GigabitEthernet1/0/24
port access vlan 900
#
interface GigabitEthernet1/0/25
shutdown
#
interface GigabitEthernet1/0/26
shutdown
#
interface GigabitEthernet1/0/27
shutdown
#
interface GigabitEthernet1/0/28
shutdown
#
ip route-static 0.0.0.0 0.0.0.0 192.168.255.242
#
snmp-agent
snmp-agent local-engineid 800063A2033897D6FC1FF0
snmp-agent sys-info version all
#
dhcp enable
#
ip https enable
#
load xml-configuration
#
user-interface aux 0
user-interface vty 0 4
authentication-mode scheme
user-interface vty 5 15
#
return
- 2019-10-31提问
- 举报
-
(0)
➤


✖
亲~登录后才可以操作哦!
确定
✖
✖
你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
✖
举报
×
侵犯我的权益
>
对根叔社区有害的内容
>
辱骂、歧视、挑衅等(不友善)
侵犯我的权益
×
侵犯了我企业的权益
>
抄袭了我的内容
>
诽谤我
>
辱骂、歧视、挑衅等(不友善)
骚扰我
侵犯了我企业的权益
×
您好,当您发现根叔知了上有关于您企业的造谣与诽谤、商业侵权等内容时,您可以向根叔知了进行举报。 请您把以下内容通过邮件发送到 pub.zhiliao@h3c.com 邮箱,我们会在审核后尽快给您答复。
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
我们认为知名企业应该坦然接受公众讨论,对于答案中不准确的部分,我们欢迎您以正式或非正式身份在根叔知了上进行澄清。
抄袭了我的内容
×
原文链接或出处
诽谤我
×
您好,当您发现根叔知了上有诽谤您的内容时,您可以向根叔知了进行举报。 请您把以下内容通过邮件发送到pub.zhiliao@h3c.com 邮箱,我们会尽快处理。
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
我们认为知名企业应该坦然接受公众讨论,对于答案中不准确的部分,我们欢迎您以正式或非正式身份在根叔知了上进行澄清。
对根叔社区有害的内容
×
垃圾广告信息
色情、暴力、血腥等违反法律法规的内容
政治敏感
不规范转载
>
辱骂、歧视、挑衅等(不友善)
骚扰我
诱导投票
不规范转载
×
举报说明



