l2tp over ipsec在hcl搞了无数次,始终不通
- 0关注
- 1收藏,2847浏览
问题描述:
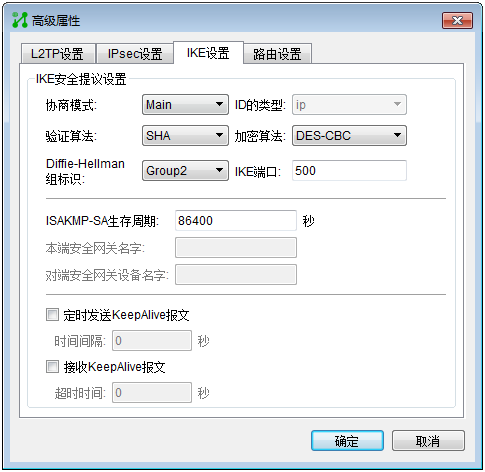
不使用ipsec加密时,l2tp 隧道能起来,能正常访问内网,使用ipsec加密后,就不能正常拔号,IKE SA协商不起来,打开DEBUG后,发现报如下错误:

组网及组网描述:
不使用ipsec加密时,l2tp 隧道能起来,能正常访问内网,使用ipsec加密后,就不能正常拔号,IKE SA协商不起来,打开DEBUG后,发现报如下错误:

- 2020-06-21提问
- 举报
-
(0)
最佳答案

一般都是设置的问题,尤其是ipsec数据流看下是否异常,封装的是否是L2TP的流量
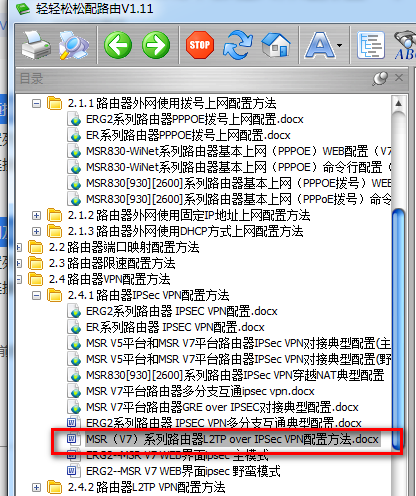
建议参考下面案例比对下:
轻轻松松配上网(路由):https://zhiliao.h3c.com/topic/huati/1247
- 2020-06-21回答
- 评论(0)
- 举报
-
(0)

详细配置如下,另外说明一下,我是照到手册搞的,那种发手册来回答问题,就不用费心了,毕竟我是想解决问题,这个实验搞了几十次都不能成功,有点不心干
<H3C>dis cur
#
version 7.1.075, Alpha 7571
#
sysname H3C
#
ip pool 1 192.168.66.2 192.168.66.200
#
system-working-mode standard
xbar load-single
password-recovery enable
lpu-type f-series
#
vlan 1
#
interface Serial1/0
#
interface Serial2/0
#
interface Serial3/0
#
interface Serial4/0
#
interface Virtual-Template1
ppp authentication-mode ms-chap ms-chap-v2 chap
remote address pool 1
ip address 192.168.66.1 255.255.255.0
#
interface Virtual-Ethernet1
#
interface NULL0
#
interface GigabitEthernet0/0
port link-mode route
combo enable copper
ip address 200.1.1.2 255.255.255.0
ipsec apply policy 1
#
interface GigabitEthernet0/1
port link-mode route
combo enable copper
ip address 192.168.1.1 255.255.255.0
#
interface GigabitEthernet0/2
port link-mode route
combo enable copper
#
interface GigabitEthernet5/0
port link-mode route
combo enable copper
#
interface GigabitEthernet5/1
port link-mode route
combo enable copper
#
interface GigabitEthernet6/0
port link-mode route
combo enable copper
#
interface GigabitEthernet6/1
port link-mode route
combo enable copper
#
scheduler logfile size 16
#
line class aux
user-role network-operator
#
line class console
user-role network-admin
#
line class tty
user-role network-operator
#
line class vty
user-role network-operator
#
line aux 0
user-role network-operator
#
line con 0
user-role network-admin
#
line vty 0 63
user-role network-operator
#
domain name system
#
domain default enable system
#
role name level-0
description Predefined level-0 role
#
role name level-1
description Predefined level-1 role
#
role name level-2
description Predefined level-2 role
#
role name level-3
description Predefined level-3 role
#
role name level-4
description Predefined level-4 role
#
role name level-5
description Predefined level-5 role
#
role name level-6
description Predefined level-6 role
#
role name level-7
description Predefined level-7 role
#
role name level-8
description Predefined level-8 role
#
role name level-9
description Predefined level-9 role
#
role name level-10
description Predefined level-10 role
#
role name level-11
description Predefined level-11 role
#
role name level-12
description Predefined level-12 role
#
role name level-13
description Predefined level-13 role
#
role name level-14
description Predefined level-14 role
#
user-group system
#
local-user h3c class network
password cipher $c$3$j1JebFHtNGqgtYf2ZpWC+BGvxYYopA==
service-type ppp
authorization-attribute user-role network-operator
#
ipsec transform-set 1
encapsulation-mode transport
esp encryption-algorithm 3des-cbc
esp authentication-algorithm md5
#
ipsec transform-set 2
encapsulation-mode transport
esp encryption-algorithm aes-cbc-128
esp authentication-algorithm sha1
#
ipsec transform-set 3
encapsulation-mode transport
esp encryption-algorithm aes-cbc-256
esp authentication-algorithm sha1
#
ipsec transform-set 4
encapsulation-mode transport
esp encryption-algorithm des-cbc
esp authentication-algorithm sha1
#
ipsec transform-set 5
encapsulation-mode transport
esp encryption-algorithm 3des-cbc
esp authentication-algorithm sha1
#
ipsec transform-set 6
encapsulation-mode transport
esp encryption-algorithm aes-cbc-192
esp authentication-algorithm sha1
#
ipsec policy-template 1 1
transform-set 1 2 3 4 5 6
ike-profile 1
#
ipsec policy 1 1 isakmp template 1
#
l2tp-group 1 mode lns
allow l2tp virtual-template 1
undo tunnel authentication
tunnel name h3c
#
l2tp enable
#
ike profile 1
keychain 1
local-identity address 200.1.1.2
match remote identity address 0.0.0.0 0.0.0.0
proposal 1 2 3 4 5 6
#
ike proposal 1
encryption-algorithm aes-cbc-128
dh group2
authentication-algorithm md5
#
ike proposal 2
encryption-algorithm 3des-cbc
dh group2
authentication-algorithm md5
#
ike proposal 3
encryption-algorithm 3des-cbc
dh group2
#
ike proposal 4
encryption-algorithm aes-cbc-256
dh group2
#
ike proposal 5
dh group2
#
ike proposal 6
encryption-algorithm aes-cbc-192
dh group2
#
ike keychain 1
pre-shared-key address 0.0.0.0 0.0.0.0 key cipher $c$3$M7SEDFcrSUgraLQRrABjeW0fWrXi2c3jDw==
#
return
- 2020-06-21回答
- 评论(0)
- 举报
-
(0)
编辑答案


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
举报
×
侵犯我的权益
×
侵犯了我企业的权益
×
- 1. 您举报的内容是什么?(请在邮件中列出您举报的内容和链接地址)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
- 3. 是哪家企业?(营业执照,单位登记证明等证件)
- 4. 您与该企业的关系是?(您是企业法人或被授权人,需提供企业委托授权书)
抄袭了我的内容
×
原文链接或出处
诽谤我
×
- 1. 您举报的内容以及侵犯了您什么权益?(请在邮件中列出您举报的内容、链接地址,并给出简短的说明)
- 2. 您是谁?(身份证明材料,可以是身份证或护照等证件)
对根叔社区有害的内容
×
不规范转载
×
举报说明



