组网及说明

组网说明:
本案例采用H3C HCL模拟器的F1060防火墙来模拟ipv4 over ipv6隧道的典型组网配置。IPV4子网和IPV6子网在网络拓扑图中已经有了明确的标识。要求IPV4子网能够穿越IPV6子网实现互通,因此需要在FW1与FW2之间建立ipv4 over ipv6隧道。
配置步骤
1、按照网络拓扑图正确配置IP地址
2、FW1与FW2建立ipv4 over ipv6隧道
特别说明:
由于本案例承载了IPV4子网及IPV6子网,因此需要在FW1、FW2的域间策略中放通IPV4及IPV6的安全策略。
配置关键点
ISP:
<H3C>sys
System View: return to User View with Ctrl+Z.
[H3C]sysname ISP
[ISP]int gi 0/0
[ISP-GigabitEthernet0/0]des <connect to FW1>
[ISP-GigabitEthernet0/0]ipv6 address 1::2 64
[ISP-GigabitEthernet0/0]quit
[ISP]int gi 0/1
[ISP-GigabitEthernet0/1]des <connect to FW2>
[ISP-GigabitEthernet0/1]ipv6 address 2::2 64
[ISP-GigabitEthernet0/1]quit
FW1:
<H3C>sys
System View: return to User View with Ctrl+Z.
[H3C]sysname FW1
[FW1]acl ipv6 basic 2001
[FW1-acl-ipv6-basic-2001]rule 0 permit source any
[FW1-acl-ipv6-basic-2001]quit
[FW1]acl basic 2002
[FW1-acl-ipv4-basic-2002]rule 0 permit source any
[FW1-acl-ipv4-basic-2002]quit
[FW1]
[FW1]zone-pair security source trust destination untrust
[FW1-zone-pair-security-Trust-Untrust]packet-filter ipv6 2001
[FW1-zone-pair-security-Trust-Untrust]packet-filter 2002
[FW1-zone-pair-security-Trust-Untrust]quit
[FW1]
[FW1]zone-pair security source untrust destination trust
[FW1-zone-pair-security-Untrust-Trust]packet-filter ipv6 2001
[FW1-zone-pair-security-Untrust-Trust]packet-filter 2002
[FW1-zone-pair-security-Untrust-Trust]quit
[FW1]
[FW1]zone-pair security source trust destination local
[FW1-zone-pair-security-Trust-Local]packet-filter ipv6 2001
[FW1-zone-pair-security-Trust-Local]packet-filter 2002
[FW1-zone-pair-security-Trust-Local]quit
[FW1]
[FW1]zone-pair security source local destination trust
[FW1-zone-pair-security-Local-Trust]packet-filter ipv6 2001
[FW1-zone-pair-security-Local-Trust]packet-filter 2002
[FW1-zone-pair-security-Local-Trust]quit
[FW1]
[FW1]zone-pair security source untrust destination local
[FW1-zone-pair-security-Untrust-Local]packet-filter ipv6 2001
[FW1-zone-pair-security-Untrust-Local]packet-filter 2002
[FW1-zone-pair-security-Untrust-Local]quit
[FW1]
[FW1]zone-pair security source local destination untrust
[FW1-zone-pair-security-Local-Untrust]packet-filter ipv6 2001
[FW1-zone-pair-security-Local-Untrust]packet-filter 2002
[FW1-zone-pair-security-Local-Untrust]quit
[FW1]
[FW1]zone-pair security source trust destination trust
[FW1-zone-pair-security-Trust-Trust]packet-filter ipv6 2001
[FW1-zone-pair-security-Trust-Trust]packet-filter 2002
[FW1-zone-pair-security-Trust-Trust]quit
[FW1]
[FW1]zone-pair security source untrust destination untrust
[FW1-zone-pair-security-Untrust-Untrust]packet-filter ipv6 2001
[FW1-zone-pair-security-Untrust-Untrust]packet-filter 2002
[FW1-zone-pair-security-Untrust-Untrust]quit
[FW1]int gi 1/0/3
[FW1-GigabitEthernet1/0/3]ip address 192.168.1.1 24
[FW1-GigabitEthernet1/0/3]quit
[FW1]int gi 1/0/2
[FW1-GigabitEthernet1/0/2]des <connect to ISP>
[FW1-GigabitEthernet1/0/2]ipv6 address 1::1 64
[FW1-GigabitEthernet1/0/2]quit
[FW1]ipv6 route-static :: 0 1::2
[FW1]security-zone name Untrust
[FW1-security-zone-Untrust]import interface GigabitEthernet 1/0/2
[FW1-security-zone-Untrust]quit
[FW1]security-zone name Trust
[FW1-security-zone-Trust]import interface GigabitEthernet 1/0/3
[FW1-security-zone-Trust]quit
FW1 ipv4 over ipv6隧道配置关键点:
[FW1]int Tunnel 0 mode ipv6
[FW1-Tunnel0]ip address 123.0.0.1 30
[FW1-Tunnel0]source 1::1
[FW1-Tunnel0]destination 2::1
[FW1-Tunnel0]quit
[FW1]ip route-static 172.16.1.0 255.255.255.0 Tunnel 0
[FW1]security-zone name Untrust
[FW1-security-zone-Untrust]import interface Tunnel 0
[FW1-security-zone-Untrust]quit
FW2:
<H3C>sys
System View: return to User View with Ctrl+Z.
[H3C]sysname FW2
[FW2]acl ipv6 basic 2001
[FW2-acl-ipv6-basic-2001]rule 0 permit source any
[FW2-acl-ipv6-basic-2001]quit
[FW2]acl basic 2002
[FW2-acl-ipv4-basic-2002]rule 0 permit source any
[FW2-acl-ipv4-basic-2002]quit
[FW2]
[FW2]zone-pair security source trust destination untrust
[FW2-zone-pair-security-Trust-Untrust]packet-filter ipv6 2001
[FW2-zone-pair-security-Trust-Untrust]packet-filter 2002
[FW2-zone-pair-security-Trust-Untrust]quit
[FW2]
[FW2]zone-pair security source untrust destination trust
[FW2-zone-pair-security-Untrust-Trust]packet-filter ipv6 2001
[FW2-zone-pair-security-Untrust-Trust]packet-filter 2002
[FW2-zone-pair-security-Untrust-Trust]quit
[FW2]
[FW2]zone-pair security source trust destination local
[FW2-zone-pair-security-Trust-Local]packet-filter ipv6 2001
[FW2-zone-pair-security-Trust-Local]packet-filter 2002
[FW2-zone-pair-security-Trust-Local]quit
[FW2]
[FW2]zone-pair security source local destination trust
[FW2-zone-pair-security-Local-Trust]packet-filter ipv6 2001
[FW2-zone-pair-security-Local-Trust]packet-filter 2002
[FW2-zone-pair-security-Local-Trust]quit
[FW2]
[FW2]zone-pair security source untrust destination local
[FW2-zone-pair-security-Untrust-Local]packet-filter ipv6 2001
[FW2-zone-pair-security-Untrust-Local]packet-filter 2002
[FW2-zone-pair-security-Untrust-Local]quit
[FW2]
[FW2]zone-pair security source local destination untrust
[FW2-zone-pair-security-Local-Untrust]packet-filter ipv6 2001
[FW2-zone-pair-security-Local-Untrust]packet-filter 2002
[FW2-zone-pair-security-Local-Untrust]quit
[FW2]
[FW2]zone-pair security source trust destination trust
[FW2-zone-pair-security-Trust-Trust]packet-filter ipv6 2001
[FW2-zone-pair-security-Trust-Trust]packet-filter 2002
[FW2-zone-pair-security-Trust-Trust]quit
[FW2]
[FW2]zone-pair security source untrust destination untrust
[FW2-zone-pair-security-Untrust-Untrust]packet-filter ipv6 2001
[FW2-zone-pair-security-Untrust-Untrust]packet-filter 2002
[FW2-zone-pair-security-Untrust-Untrust]quit
[FW2]int gi 1/0/3
[FW2-GigabitEthernet1/0/3]ip address 172.16.1.1 24
[FW2-GigabitEthernet1/0/3]quit
[FW2]int gi 1/0/2
[FW2-GigabitEthernet1/0/2]des <connect to ISP>
[FW2-GigabitEthernet1/0/2]ipv6 address 2::1 64
[FW2-GigabitEthernet1/0/2]quit
[FW2]ipv6 route-static :: 0 2::2
[FW2]security-zone name Trust
[FW2-security-zone-Trust]import interface GigabitEthernet 1/0/3
[FW2-security-zone-Trust]quit
[FW2]security-zone name Untrust
[FW2-security-zone-Untrust]import interface GigabitEthernet 1/0/2
[FW2-security-zone-Untrust]quit
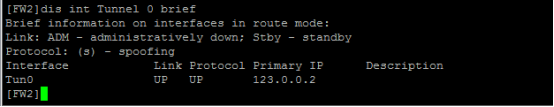
FW2 ipv4 over ipv6隧道关键配置点:
[FW2]int Tunnel 0 mode ipv6
[FW2-Tunnel0]ip address 123.0.0.2 30
[FW2-Tunnel0]source 2::1
[FW2-Tunnel0]destination 1::1
[FW2-Tunnel0]quit
[FW2]ip route-static 192.168.1.0 255.255.255.0 123.0.0.1
[FW2]security-zone name Untrust
[FW2-security-zone-Untrust]import interface Tunnel 0
[FW2-security-zone-Untrust]quit
测试:
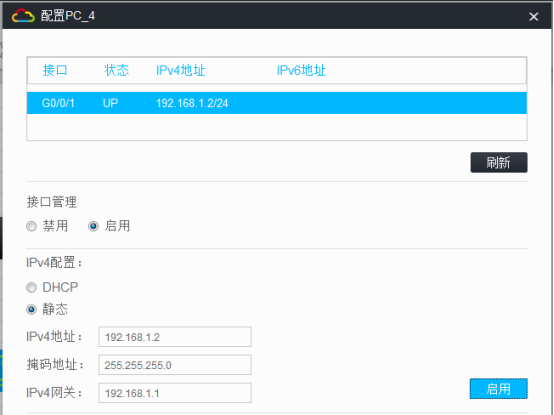
所有PC都填写IP地址:

IPV4子网1的PC可以PING通IPV4子网2的PC:
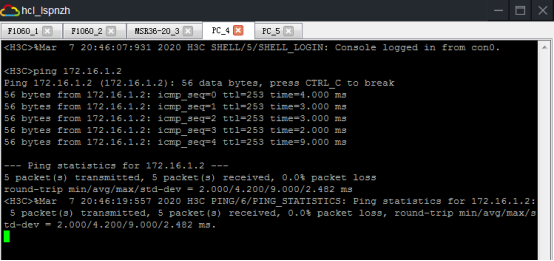
IPV4子网2的PC可以PING通IPV4子网1的PC:

根据测试结果得知,IPV4子网1和IPV4子网2均可穿越IPV6子网实现互通。
分别查看FW1、FW2的隧道状态及信息:

分别查看FW1、FW2的路由表,均可看到隧道的路由:


至此,F1060 ipv4 over ipv6隧道典型组网配置案例已完成!
该案例暂时没有网友评论
编辑评论
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
