组网及说明
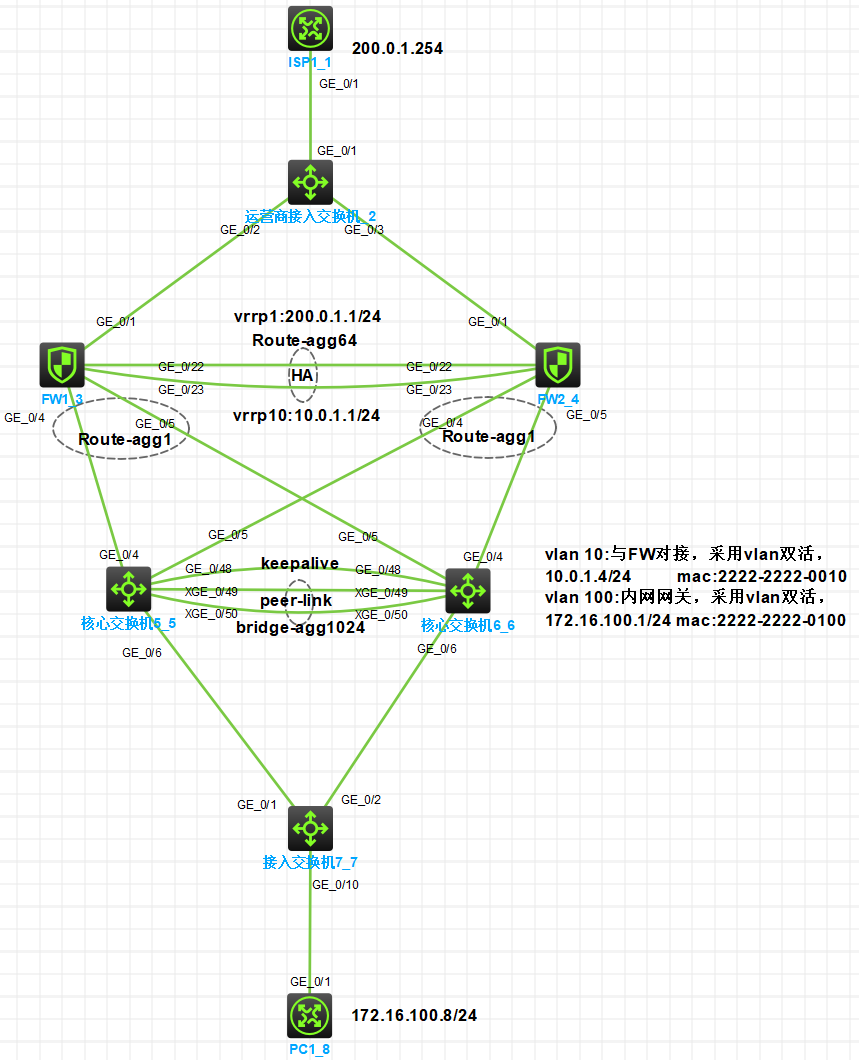
一、拓扑
二、需求
1、
2、
3、
4、
5、
三、配置思路
1、
2、
3、
4、
四、接口及地址规划
|
本端接口 |
vlan/ip |
补充 |
对端 |
|
运营商接入交换机 |
|||
|
G1/0/1 |
VLAN10 |
ISP1 |
ISP1 |
|
G1/0/2 |
VLAN10 |
|
FW1:G1/0/1 |
|
G1/0/3 |
VLAN10 |
|
FW2:G1/0/1 |
|
出口防火墙FW1 |
|||
|
G1/0/1 |
10.0.0.1/30 |
VRRP1:200.0.1.1/24 active |
运营商接入:G1/0/2 |
|
G1/0/4 |
Route-agg1 10.0.1.2/24 |
VRRP10:10.0.1.1/24 active |
核心交换机5G1/0/4 |
|
G1/0/5 |
核心交换机6:G1/0/5 |
||
|
G1/0/22 |
Route-agg64,1.1.1.1/30 |
HA接口 |
FW2:G1/0/22 |
|
G1/0/23 |
FW2:G1/0/23 |
||
|
出口防火墙FW2 |
|||
|
G1/0/1 |
10.0.0.2/30 |
VRRP1:200.0.1.1/24 active |
运营商接入:G1/0/3 |
|
G1/0/4 |
Route-agg1 10.0.1.3/24 |
VRRP10:10.0.1.1/24 active |
核心交换机5G1/0/5 |
|
G1/0/5 |
核心交换机6:G1/0/4 |
||
|
G1/0/22 |
Route-agg64,1.1.1.2/30 |
HA接口 |
FW1:G1/0/22 |
|
G1/0/23 |
FW1:G1/0/23 |
||
|
核心交换机5 |
|||
|
XG1/0/49 |
Bridge-agg100 |
Peer-link |
核心交换机6:XG1/0/49 |
|
XG1/0/52 |
核心交换机6:XG1/0/50 |
||
|
G1/0/48 |
1.1.1.5/30 |
VRF:mlag keepalive |
核心交换机6:G1/0/48 |
|
G1/0/4 |
Bridge-agg1 m-lag group1 |
Vlan-int10: 10.0.1.4/24 2222-2222-0010 |
FW1:G1/0/4 |
|
G1/0/5 |
Bridge-agg2 m-lag group2 |
FW2:G1/0/4 |
|
|
G1/0/6 |
Bridge-agg100 m-lag group100 |
Vlan-int100: 172.16.100.1/24 2222-2222-0100 |
接入交换机:G1/0/1 |
|
核心交换机6 |
|||
|
XG1/0/49 |
Bridge-agg100 |
Peer-link |
核心交换机5:XG1/0/49 |
|
XG1/0/52 |
|
|
核心交换机5:XG1/0/50 |
|
G1/0/48 |
1.1.1.6/30 |
VRF:mlag keepalive |
核心交换机5:G1/0/48 |
|
G1/0/4 |
Bridge-agg2 m-lag group2 |
Vlan-int10: 10.0.1.4/24 2222-2222-0010 |
FW2:G1/0/5 |
|
G1/0/5 |
Bridge-agg1 m-lag group1 |
FW1:G1/0/5 |
|
|
G1/0/6 |
Bridge-agg100 m-lag group100 |
Vlan-int100: 172.16.100.1/24 2222-2222-0100 |
接入交换机:G1/0/2 |
|
接入交换机 |
|||
|
G1/0/1 |
Bridge-agg100 VLAN100 |
Trunk |
核心交换机5:G1/0/6 |
|
G1/0/2 |
核心交换机6:G1/0/6 |
||
|
G1/0/10 |
Access Vlan100 |
|
PC1 |
|
终端 |
|||
|
PC1 |
172.16.100.8/24 |
|
接入交换机:G1/0/10 |
配置步骤
HCL模拟器工程文件已上传至HCLhub:http://hclhub.h3c.com/project/9496/summary/master?path=README.md&type=text
如连接失效可登录http://hclhub.h3c.com/ 搜索:v7fw_rbm_vrrp_主备_to_mlag
一、配置步骤
(1)
1、
|
#创建vlan10,并将接口g1/0/1~g1/0/3划分到vlan10 # system-view # vlan 10 port GigabitEthernet 1/0/1 GigabitEthernet 1/0/2 GigabitEthernet 1/0/3 quit # #保存配置 save force |
(2)
1、
|
#创建三层聚合口64,并将接口g1/0/22和接口g1/0/23加入该聚合口。该聚合口将作为FW之间RBM的数据/控制通道,同时为接口配置控制通道IP。 # system-view # sysname FW1 # interface Route-Aggregation64 ip address 1.1.1.1 255.255.255.252 # interface GigabitEthernet1/0/22 port link-aggregation group 64 # interface GigabitEthernet1/0/23 port link-aggregation group 64 #完成RBM配置,指定数据通道为Route-Aggregation64,HA回切时间为10分钟,控制通道本段ip地址为1.1.1.1,对端ip地址为1.1.1.2,本设备作为主管理设备。 remote-backup group data-channel interface Route-Aggregation64 delay-time 10 local-ip 1.1.1.1 remote-ip 1.1.1.2 device-role primary # |
|
#FW2此部分配置与FW1类似。 # system-view # sysname FW2 # interface Route-Aggregation64 ip address 1.1.1.2 255.255.255.252 # interface GigabitEthernet1/0/22 port link-aggregation group 64 # interface GigabitEthernet1/0/23 port link-aggregation group 64 # remote-backup group data-channel interface Route-Aggregation64 delay-time 10 local-ip 1.1.1.2 remote-ip 1.1.1.1 device-role secondary # |
2、
|
#ISP只提供了1个公网ip,所以防火墙上行连接到同一组ISP的接口可配置同网段的私网ip地址,将vrrp虚拟地址配置为ISP的ip地址即可,注意配置虚拟IP时需要配置掩码,掩码以ISP给的为准。 #配置VRRP时需要与RBM关联(主设备命令后增加active,反之standby) # interface GigabitEthernet1/0/1 port link-mode route ip address 10.0.0.1 255.255.255.252 vrrp vrid 1 virtual-ip 200.0.1.1 255.255.255.0 active # interface Route-Aggregation1 ip address 10.0.1.2 255.255.255.0 link-aggregation mode dynamic vrrp vrid 10 virtual-ip 10.0.1.1 255.255.255.0 active # interface GigabitEthernet1/0/4 port link-aggregation group 1 # interface GigabitEthernet1/0/5 port link-aggregation group 1 # |
|
#FW2此部分配置与FW1类似。 # interface GigabitEthernet1/0/1 port link-mode route ip address 10.0.0.2 255.255.255.252 vrrp vrid 1 virtual-ip 200.0.1.1 255.255.255.0 standby # # interface Route-Aggregation1 ip address 10.0.1.2 255.255.255.0 link-aggregation mode dynamic vrrp vrid 10 virtual-ip 10.0.1.1 255.255.255.0 standby # interface GigabitEthernet1/0/4 port link-aggregation group 1 # interface GigabitEthernet1/0/5 port link-aggregation group 1 # |
3、
|
#配置缺省路由,同时配置去往内网vlan100的回程路由 # ip route-static 0.0.0.0 0 200.0.1.254 ip route-static 172.16.100.0 24 10.0.1.4 # |
|
#FW2此部分配置与FW1类似。 # ip route-static 0.0.0.0 0 200.0.1.254 ip route-static 172.16.100.0 24 10.0.1.4 # |
4、
|
#配置将内网接口Route-Aggregation1加入trust区域,将ISP1接口g1/0/1加入untrust区域。 # security-zone name Trust import interface Route-Aggregation1 quit # security-zone name Untrust import interface GigabitEthernet1/0/1 quit # |
5、
|
#配置nat地址组,用于源地址转换,同时各地址组与接口的VRRP备份组关联 # nat address-group 1 name isp1 address 200.0.1.1 200.0.1.1 vrrp vrid 1 quit # nat global-policy #配置名为trust2isp的规则,用于匹配由trust域访问untrust域,源地址是172.16.100.0/24的流量,匹配上后执行源地址转换,转换后的源ip为nat地址组1 中的地址。 rule name trust2isp source-zone trust destination-zone untrust source-ip subnet 172.16.100.0 24 action snat address-group 1 vrrp 1 |
6、
|
# security-policy ip #创建名为trust2untrust的安全策略规则rule 5,匹配源域为trust,目的域为untrust或untrust2,源地址为172.16.100.0/24的流量,动作为允许。(对应内网vlan100访问互联网的需求) rule 5 name trust2untrust action pass source-zone trust destination-zone untrust source-ip-subnet 172.16.100.0 255.255.255.0 # #保存配置 #save force |
(3)
1、
|
核心交换机5 |
核心交换机6 |
说明 |
|
system-view |
system-view |
进入系统视图 |
|
m-lag system-mac 9690-857f-0500 |
m-lag system-mac 9690-857f-0500 |
配置m-lag系统mac,两台设备一致 |
|
m-lag system-number 1 |
m-lag system-number 2 |
配置m-lag系统编号,两台设备不一致 |
|
m-lag system-priority 123 |
m-lag system-priority 123 |
配置m-lag系统优先级,两台设备一致 |
|
m-lag standalone enable |
m-lag standalone enable |
开启m-lag设备独立工作模式 |
|
ip vpn-instance mlag |
ip vpn-instance mlag |
创建vpn实例m-lag |
|
description mlagkeepalive |
description mlagkeepalive |
描述 |
|
quit |
quit |
|
|
interface GigabitEthernet1/0/48 |
interface GigabitEthernet1/0/48 |
进入接口g1/0/48 |
|
port link-mode route |
port link-mode route |
接口切换到三层模式 |
|
y |
y |
|
|
ip binding vpn-instance mlag |
ip binding vpn-instance mlag |
绑定vpn实例mlag |
|
ip address 1.1.1.5 255.255.255.252 |
ip address 1.1.1.5 255.255.255.252 |
配置ip地址 |
|
quit |
quit |
|
|
m-lag keepalive ip destination 1.1.1.6 source 1.1.1.5 vpn-instance mlag |
m-lag keepalive ip destination 1.1.1.5 source 1.1.1.6 vpn-instance mlag |
配置m-lag keepalive参数 |
|
interface Bridge-Aggregation1024 |
interface Bridge-Aggregation1024 |
创建聚合口bridge-agg1024 |
|
link-aggregation mode dynamic |
link-aggregation mode dynamic |
配置聚合口为动态模式 |
|
quit |
quit |
|
|
inter range Ten-GigabitEthernet 1/0/49 to1/0/50 |
inter range Ten-GigabitEthernet 1/0/49 to1/0/50 |
批量进入接口xg1/0/49和xg1/0/50视图 |
|
port link-aggregation group 1024 |
port link-aggregation group 1024 |
将接口加入聚合组1024 |
|
quit |
quit |
|
|
interface Bridge-Aggregation1024 |
interface Bridge-Aggregation1024 |
进入聚合口bridge-agg1024 |
|
port m-lag peer-link 1 |
port m-lag peer-link 1 |
配置聚合口作为peer-link口 |
|
undo mac-address static source-check enable |
undo mac-address static source-check enable |
关闭报文入接口与静态MAC地址表项匹配检查功能,避免跨peer-link链路三层转发的流量不通,真机需配置,模拟器不用 |
|
jumboframe enable 1552 |
jumboframe enable 1552 |
模拟器需配置,真机不用 |
|
Quit |
Quit |
|
2、
|
核心交换机5 |
核心交换机6 |
说明 |
|
Vlan 10 100 |
Vlan 10 100 |
创建vlan10和100 |
|
quit |
quit |
|
|
interface Bridge-Aggregation1 |
interface Bridge-Aggregation1 |
创建二层聚合口bridge-agg1 |
|
link-aggregation mode dynamic |
link-aggregation mode dynamic |
配置聚合接口为动态模式 |
|
port m-lag group 1 |
port m-lag group 1 |
配置聚合口加入m-lag组1 |
|
quit |
quit |
|
|
interface Bridge-Aggregation2 |
interface Bridge-Aggregation2 |
创建二层聚合口bridge-agg2 |
|
link-aggregation mode dynamic |
link-aggregation mode dynamic |
配置聚合接口为动态模式 |
|
port m-lag group 2 |
port m-lag group 2 |
配置聚合口加入m-lag组2 |
|
quit |
quit |
|
|
interface Bridge-Aggregation100 |
interface Bridge-Aggregation100 |
创建二层聚合口bridge-agg100 |
|
link-aggregation mode dynamic |
link-aggregation mode dynamic |
配置聚合接口为动态模式 |
|
port m-lag group 100 |
port m-lag group 100 |
配置聚合口加入m-lag组100 |
|
quit |
quit |
|
|
interface GigabitEthernet1/0/4 |
interface GigabitEthernet1/0/5 |
进入接口视图 |
|
port link-aggregation group 1 |
port link-aggregation group 1 |
配置接口加入聚合组1 |
|
Quit |
Quit |
|
|
interface GigabitEthernet1/0/5 |
interface GigabitEthernet1/0/4 |
进入接口视图 |
|
port link-aggregation group 2 |
port link-aggregation group 2 |
配置接口加入聚合组2 |
|
Quit |
Quit |
|
|
interface GigabitEthernet1/0/6 |
interface GigabitEthernet1/0/6 |
进入接口视图 |
|
port link-aggregation group 100 |
port link-aggregation group 100 |
配置接口加入聚合组100 |
|
Quit |
Quit |
|
|
interface Bridge-Aggregation1 |
interface Bridge-Aggregation1 |
进入聚合组视图 |
|
port access vlan 10 |
port access vlan 10 |
配置接口划分到vlan10 |
|
Quit |
Quit |
|
|
interface Bridge-Aggregation2 |
interface Bridge-Aggregation2 |
进入聚合组视图 |
|
port access vlan 10 |
port access vlan 10 |
配置接口划分到vlan10 |
|
Quit |
Quit |
|
|
interface Bridge-Aggregation100 |
interface Bridge-Aggregation100 |
进入聚合组视图 |
|
port link-type trunk |
port link-type trunk |
配置聚合口为trunk模式 |
|
port trunk permit vlan 100 |
port trunk permit vlan 100 |
配置聚合口允许vlan100通过 |
|
Quit |
Quit |
|
|
interface Vlan-interface10 |
interface Vlan-interface10 |
创建vlan-int10 |
|
ip address 10.0.1.4 255.255.255.0 |
ip address 10.0.1.4 255.255.255.0 |
配置ip地址 |
|
mac-address 2222-2222-0010 |
mac-address 2222-2222-0010 |
配置mac地址 |
|
Quit |
Quit |
|
|
interface Vlan-interface100 |
interface Vlan-interface100 |
创建vlan-int100 |
|
ip address 172.16.100.1 255.255.255.0 |
ip address 172.16.100.1 255.255.255.0 |
配置ip地址 |
|
mac-address 2222-2222-0100 |
mac-address 2222-2222-0100 |
配置mac地址 |
|
quit |
quit |
|
|
ip route-static 0.0.0.0 0 10.0.1.1 |
ip route-static 0.0.0.0 0 10.0.1.1 |
配置缺省路由 |
|
m-lag mad exclude interface GigabitEthernet1/0/48 |
m-lag mad exclude interface GigabitEthernet1/0/48 |
配置keepalive接口为m-lag的mad保留接口 |
|
m-lag mad exclude interface Vlan-interface10 |
m-lag mad exclude interface Vlan-interface10 |
配置vlan-int接口为m-lag的mad保留接口 |
|
m-lag mad exclude interface Vlan-interface100 |
m-lag mad exclude interface Vlan-interface100 |
配置vlan-int接口为m-lag的mad保留接口 |
|
Save force |
Save force |
|
(4)
1、
|
#创建业务vlan100 # system-view # sysname Acccesssw # vlan 100 # #配置二层聚合口100,将上行接口g1/0/1和g1/0/2加入二层聚合口100,同时放行vlan100。这里需要按照:创建聚合口、接口空配加入聚合口、进入聚合口完成vlan配置的顺序操作。 # interface Bridge-Aggregation100 quit # interface range GigabitEthernet 1/0/1 GigabitEthernet1/0/2 port link-aggregation group 100 quit # interface Bridge-Aggregation100 port link-type trunk port trunk permit vlan 100 # #配置下行接终端的接口加入vlan100,并开启stp边缘端口 # interface GigabitEthernet1/0/10 port access vlan 100 stp edged-port # #保存配置 save force |
二、结果验证
1、
|
#FW1: RBM_P<FW1>dis remote-backup-group status Remote backup group information: Backup mode: Active/standby -----------备份组模式为主/备 Device management role: Primary-----------设备管理状态为主 Device running status: Active -----------设备运行状态为主 Data channel interface: Route-Aggregation64 Local IP: 1.1.1.1 Remote IP: 1.1.1.2 Destination port: 60064 Control channel status: Connected Keepalive interval: 1s Keepalive count: 10 Configuration consistency check interval: 24 hour Configuration consistency check result: Not Performed Configuration backup status: Auto sync enabled Session backup status: Hot backup enabled Delay-time: 10 min Uptime since last switchover: 0 days, 1 hours, 55 minutes Switchover records: Time Status change Cause 2023-02-27 17:35:28 Active to Active Keepalive link established
RBM_P<FW1> dis vrrp IPv4 Virtual Router Information: Running mode : Standard RBM control channel is established VRRP active group status : Master VRRP standby group status: Master Total number of virtual routers : 2 Interface VRID State Running Adver Auth Virtual Pri Timer Type IP ---------------------------------------------------------------------------- GE1/0/1 1 Master 100 100 Not supported 200.0.1.1 RAGG1 10 Master 100 100 Not supported 10.0.1.1 |
|
#FW2: RBM_S<FW2>dis remote-backup-group status Remote backup group information: Backup mode: Active/standby Device management role: Secondary Device running status: Standby Data channel interface: Route-Aggregation64 Local IP: 1.1.1.2 Remote IP: 1.1.1.1 Destination port: 60064 Control channel status: Connected Keepalive interval: 1s Keepalive count: 10 Configuration consistency check interval: 24 hour Configuration consistency check result: Not Performed Configuration backup status: Auto sync enabled Session backup status: Hot backup enabled Delay-time: 10 min Uptime since last switchover: 0 days, 1 hours, 57 minutes Switchover records: Time Status change Cause 2023-02-27 17:35:27 Active to Standby Keepalive link established RBM_S<FW2> RBM_S<FW2>dis vrrp IPv4 Virtual Router Information: Running mode : Standard RBM control channel is established VRRP active group status : Backup VRRP standby group status: Backup Total number of virtual routers : 2 Interface VRID State Running Adver Auth Virtual Pri Timer Type IP ---------------------------------------------------------------------------- GE1/0/1 1 Backup 100 100 Not supported 200.0.1.1 RAGG1 10 Backup 100 100 Not supported 10.0.1.1 |
2、
|
[Coresw1]dis m-lag summary Flags: A -- Aggregate interface down, B -- No peer M-LAG interface configured C -- Configuration consistency check failed
Peer-link interface: BAGG1024 Peer-link interface state (cause): UP Keepalive link state (cause): UP
M-LAG interface information M-LAG IF M-LAG group Local state (cause) Peer state Remaining down time(s) BAGG1 1 UP UP - BAGG2 2 UP UP - BAGG100 100 UP UP - [Coresw1] [Coresw1]dis m-lag keepalive Neighbor keepalive link status (cause): Up Neighbor is alive for: 7037 s 934 ms Keepalive packet transmission status: Sent: Successful Received: Successful Last received keepalive packet information: Source IP address: 1.1.1.6 Time: 2023/02/27 19:33:16 Action: Accept
M-LAG keepalive parameters: Destination IP address: 1.1.1.6 Source IP address: 1.1.1.5 Keepalive UDP port : 6400 Keepalive VPN name : mlag Keepalive interval : 1000 ms Keepalive timeout : 5 sec Keepalive hold time: 3 sec [Coresw1] |
3、
|
<PC1>ping 200.0.1.254 Ping 200.0.1.254 (200.0.1.254): 56 data bytes, press CTRL+C to break 56 bytes from 200.0.1.254: icmp_seq=0 ttl=253 time=1.649 ms 56 bytes from 200.0.1.254: icmp_seq=1 ttl=253 time=1.313 ms 56 bytes from 200.0.1.254: icmp_seq=2 ttl=253 time=1.110 ms 56 bytes from 200.0.1.254: icmp_seq=3 ttl=253 time=1.091 ms 56 bytes from 200.0.1.254: icmp_seq=4 ttl=253 time=1.845 ms
--- Ping statistics for 200.0.1.254 --- 5 packet(s) transmitted, 5 packet(s) received, 0.0% packet loss round-trip min/avg/max/std-dev = 1.091/1.402/1.845/0.299 ms <PC1> <PC1>%Feb 27 19:37:48:239 2023 PC1 PING/6/PING_STATISTICS: Ping statistics for 200.0.1.254: 5 packet(s) transmitted, 5 packet(s) received, 0.0% packet loss, round-trip min/avg/max/std-dev = 1.091/1.402/1.845/0.299 ms. <PC1> |
配置关键点
1、ISP只提供了1个公网ip,所以防火墙上行连接到同一组ISP的接口可配置同网段的私网ip地址,将vrrp虚拟地址配置为ISP的ip地址即可,注意配置虚拟IP时需要配置掩码,掩码以ISP给的为准。
2、配置VRRP时需要与RBM关联(主设备命令后增加active,反之standby)
你好,不知为何,m-lag 的成员接口 bri,1,2,100 都无法建立成功,并没有修改过配置

- 2023-06-20回答
- 评论(1)
- 举报
-
(0)
新版模拟器m-lag有问题,把这两条配上去: m-lag consistency-check mode loose(配置M-LAG配置一致性检查的模式为松散模式) m-lag consistency-check disable( 关闭M-LAG配置一致性检查功能)
你好,双活网关配置主备两条链路都跑流量吗?做了一下测试,看了流统好像只有一边有报文
- 2023-07-25回答
- 评论(1)
- 举报
-
(0)
是两边都跑的,可以多找几条流测试,数量少了效果不明显。
ISP单公网IP 做SLL VPN 是否可以正常实现
- 2023-08-07回答
- 评论(1)
- 举报
-
(0)
RBM+VRRP主备,单公网ip,支持sslvpn,在管理主设备上正常配置就行.

这里为什么m-lag要开启独立工作模式?
- 2023-08-24回答
- 评论(1)
- 举报
-
(0)
当M-LAG系统分裂时,为避免出现M-LAG系统中的两台设备都作为主设备转发流量的情况,可开启独立模式,使M-LAG设备立即或经过一段时间切换到独立运行模式。M-LAG设备切换到独立运行模式后,聚合接口发送的LACP报文中携带的M-LAG系统参数还原为聚合接口的LACP系统MAC地址和LACP优先级,使同一M-LAG组中的两个聚合接口的LACP系统MAC地址和LACP优先级不一致。这样只有一边聚合接口的成员端口可以被选中,被选中的设备独立运行转发业务流量,避免流量转发异常。
在模拟器模拟m-lag,聚合口下配置DR口,将物理接口加入聚合口后,聚合成员端口一直down,是模拟器问题吗?
- 2023-10-26回答
- 评论(1)
- 举报
-
(0)
关闭配置一致性检查
<fw>ping不通isp地址 有办法解决?
[fw] ip route-static 0.0.0.0 0 isp地址,因为下一跳不可达,查看路由表根本没有,有办法解决? (我试过加permanent才行)
你这个方案验证过吗?怎么这么不靠谱呢?
- 2023-10-27回答
- 评论(1)
- 举报
-
(0)
我不认为我的方案有问题,验证过的,我的环境不用你说的这个参数。
编辑评论
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作


不管主设备还是备设备响应网关的arp请求,终端得到的mac都是一样的,因此当网关所在的任意mlag成员设备故障时,可以实现了终端无感知。