DVPN V7 MSR G2 hub V5 SR6608 spoke
- 0关注
- 0收藏 1431浏览
部MSR3620做DVPN HUB和VAM Server,分支点使用Comware v5的SR6608和ICG2000做Spoke和VAM client,Spoke和HUB自动建立VPN,为了数据安全,使用IPSec保护VPN数据流。私网路由通过OSPF自动学习。
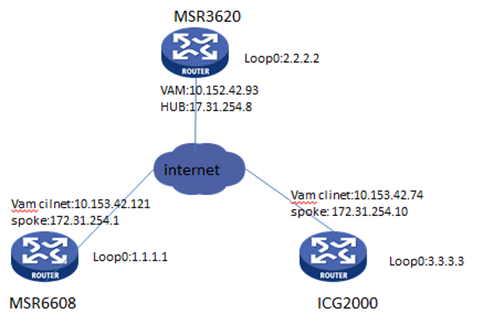
部MSR3620做DVPN HUB和VAM Server,分支点使用Comware v5的SR6608和ICG2000做Spoke和VAM client,Spoke和HUB自动建立VPN,为了数据安全,使用IPSec保护VPN数据流。私网路由通过OSPF自动学习。
MSR3620配置
#配置接口地址
interface LoopBack0
ip address 2.2.2.2 255.255.255.255
#
interface GigabitEthernet0/0
ip address 10.153.42.93 255.255.255.0
#配置VAM服务器domain为123,指定hub地址为172.31.254.8,spoke的地址访问为172.31.254.0 172.31.254.255。
vam server advpn-domain 123 id 1
pre-shared-key cipher $c$3$pd9mir37LpNvYevgHk+RfUfNRkyoxA==
authentication-method none
server enable
hub-group 0
hub private-address 172.31.254.8
spoke private-address range 172.31.254.0 172.31.254.255
#配置vam客户端名称hangzhou,指定注册服务器为10.153.42.93
vam client name hangzhou
advpn-domain 123
server primary ip-address 10.153.42.93
pre-shared-key cipher $c$3$BPfl3/wjrPgLJaFNbkaq6bH/CFAAFA==
client enable
#配置ospf,使能loop0口和tunnel口。
ospf 1
area 0.0.0.0
network 2.2.2.2 0.0.0.0
network 172.31.254.8 0.0.0.0
#配置ike密钥链,命名为dvpn
ike keychain dvpn
pre-shared-key address 0.0.0.0 0.0.0.0 key cipher $c$3$/BzI9UeIR8cTXqq9Azx2DlVDnLcANw==
#配置ike profile,关联之前配置的密钥链
ike profile dvpn
keychain dvpn
#配置IPSec框架
ipsec transform-set dvpn
encapsulation-mode transport
esp encryption-algorithm des-cbc
esp authentication-algorithm sha1
#
ipsec profile dvpn isakmp
transform-set dvpn
ike-profile dvpn
#配置tunnel口,OSPF网络类型指定p2mp,关联IPSec策略,绑定vam client使能兼容模式。
interface Tunnel1 mode advpn gre
ip address 172.31.254.8 255.255.255.0
ospf network-type p2mp
source GigabitEthernet0/0
tunnel protection ipsec profile dvpn
vam client hangzhou compatible advpn0
#配置默认路由指向外网网关
ip route-static 0.0.0.0 0.0.0.0 10.153.42.1
ICG2000配置
#配置互联口地址
interface Ethernet0/0
port link-mode route
ip address 10.153.42.74 255.255.255.0
#
interface LoopBack0
ip address 3.3.3.3 255.255.255.255
#配置vam client,命名为shanghai,指定服务器为10.153.42.93,vpn域名称和MSR3620 advpn-domain一致。
vam client name shanghai
client enable
server primary ip-address 10.153.42.93
vpn 123
pre-shared-key simple 123
#IPSec相关配置
ike peer dvpn
pre-shared-key simple 123
#
ipsec proposal dvpn
encapsulation-mode transport
esp authentication-algorithm sha1
#
ipsec profile dvpn
ike-peer dvpn
proposal dvpn
#配置tunnel口,OSPF网络类型指定p2mp,关联IPSec策略,绑定vam client。
interface Tunnel1
ip address 172.31.254.10 255.255.255.0
tunnel-protocol dvpn gre
source Ethernet0/0
ospf network-type p2mp
ipsec profile dvpn
vam client shanghai
#配置OSPF,使能loop0口和tunnel口。
ospf 1
area 0.0.0.0
network 3.3.3.3 0.0.0.0
network 172.31.254.10 0.0.0.0
#配置指向外网网关的默认路由
ip route-static 0.0.0.0 0.0.0.0 10.153.42.1
SR6608配置
#配置接口地址
interface LoopBack0
ip address 1.1.1.1 255.255.255.255
#
interface GigabitEthernet0/0/0
ip address 10.153.42.121 255.255.255.0
#配置vam client,命名为beijing,指定服务器为10.153.42.93,vpn域名名称和MSR3620 advpn-domain名一致。
vam client name beijing
client enable
server primary ip-address 10.153.42.93
vpn 123
pre-shared-key cipher $c$3$Y24eXo6wWvzRLpL5FBaNUh/ewGcE1Q==
#配置IPSec相关配置
ike peer vam
pre-shared-key cipher $c$3$cw8tajh6I/67q11FiwF4js4I2cg+7g==
#
ipsec transform-set vam
encapsulation-mode transport
transform esp
esp authentication-algorithm sha1
esp encryption-algorithm des
#
ipsec profile vam
ike-peer vam
transform-set vam
#配置tunnel口,OSPF网络类型指定p2mp,关联IPSec策略,绑定vam client。
interface Tunnel1
ip address 172.31.254.1 255.255.255.0
tunnel-protocol dvpn gre
source M-GigabitEthernet0/0/0
ospf network-type p2mp
ipsec profile vam
vam client beijing
#配置OSPF,使能loop0口和tunnel口。
ospf 1
area 0.0.0.0
network 172.31.254.1 0.0.0.0
network 1.1.1.1 0.0.0.0
#配置指向外网网关的默认路由
ip route-static 0.0.0.0 0.0.0.0 10.153.42.1
#
结果验证
<MSR3620>disp vam ser add
ADVPN domain name: 123
Total private address mappings: 3
Group Private address Public address Type NAT Holding time
0 172.31.254.1 10.153.42.121 Spoke No 1H 17M 48S
0 172.31.254.8 10.153.42.93 Hub No 1H 23M 12S
0 172.31.254.10 10.153.42.74 Spoke No 1H 22M 53S
<H3C>ping -a 2.2.2.2 1.1.1.1
Ping 1.1.1.1 (1.1.1.1) from 2.2.2.2: 56 data bytes, press CTRL_C to break
56 bytes from 1.1.1.1: icmp_seq=0 ttl=255 time=0.528 ms
56 bytes from 1.1.1.1: icmp_seq=1 ttl=255 time=0.452 ms
56 bytes from 1.1.1.1: icmp_seq=2 ttl=255 time=0.456 ms
56 bytes from 1.1.1.1: icmp_seq=3 ttl=255 time=0.412 ms
56 bytes from 1.1.1.1: icmp_seq=4 ttl=255 time=0.423 ms
--- Ping statistics for 1.1.1.1 ---
5 packets transmitted, 5 packets received, 0.0% packet loss
round-trip min/avg/max/std-dev = 0.412/0.454/0.528/0.041 ms
<H3C>ping -a 2.2.2.2 3.3.3.3
Ping 3.3.3.3 (3.3.3.3) from 2.2.2.2: 56 data bytes, press CTRL_C to break
56 bytes from 3.3.3.3: icmp_seq=0 ttl=255 time=1.978 ms
56 bytes from 3.3.3.3: icmp_seq=1 ttl=255 time=1.945 ms
56 bytes from 3.3.3.3: icmp_seq=2 ttl=255 time=1.884 ms
56 bytes from 3.3.3.3: icmp_seq=3 ttl=255 time=2.221 ms
56 bytes from 3.3.3.3: icmp_seq=4 ttl=255 time=2.198 ms
--- Ping statistics for 3.3.3.3 ---
5 packets transmitted, 5 packets received, 0.0% packet loss
round-trip min/avg/max/std-dev = 1.884/2.045/2.221/0.138 ms
1、MSR G2和V5设备建立DVPN时tunnel绑定vam client 时必须使用 compatible advpn0,必然建立失败,debug可以看到如下提示。
<MSR3620>debugging advpn all
*Jan 17 18:10:25:657 2015 H3C ADVPN/7/EVENT: Compatibility was not configured.
2、MSR G2的advpn-domain名称和V5 VAM client下配置了VPN域名保证一致。
✖
案例意见反馈


亲~登录后才可以操作哦!
确定你的邮箱还未认证,请认证邮箱或绑定手机后进行当前操作
